AI-Powered SIEM: Reducing Alert Fatigue for SOC Analysts
Discover how AI-powered SIEMs reduce alert fatigue for SOC analysts. Learn how machine learning automates threat triage and correlation for faster response.
Introduction: The Crisis in the SOC
In the previous article, we discussed how UEBA helps identify anomalous human and machine behavior. However, UEBA is just one feed of information. In a modern enterprise, firewalls, endpoints, identity providers, and cloud infrastructure generate billions of logs every day.
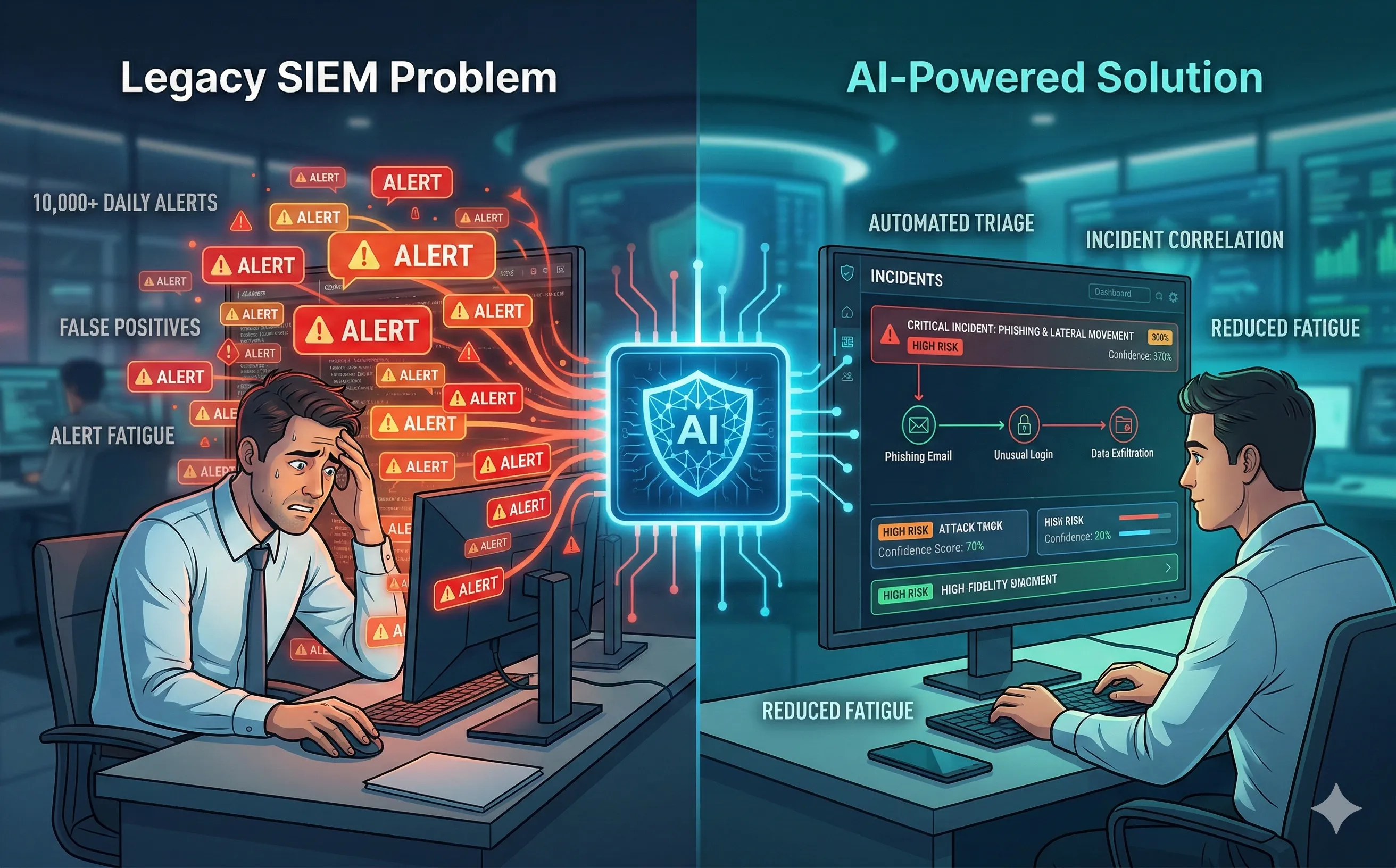
These logs are centralized in a Security Information and Event Management (SIEM) system. For years, the SIEM has been the beating heart of the Security Operations Center (SOC). But it has also become a source of immense stress. Legacy SIEMs rely on static correlation rules that generate thousands of low-fidelity alerts daily. This creates Alert Fatigue—a dangerous psychological phenomenon where overwhelmed analysts begin ignoring alerts, inevitably missing the real attack hidden in the noise. AI-powered SIEMs are emerging as the critical solution to this data crisis.
1. The Legacy SIEM Problem: Finding a Needle in a Field of Needles
Traditional SIEMs are essentially massive search engines for logs. If an administrator sets a rule like “Alert on 5 failed logins,” the SIEM will blindly fire an alert every time that condition is met, regardless of context.
- False Positives: A misconfigured service account with an expired password might trigger 500 alerts in an hour. An analyst has to manually review and close each one.
- Burnout: The industry average time to investigate a single alert is 10 to 15 minutes. When a SOC receives 10,000 alerts a day, it is mathematically impossible for the human team to investigate them all, a problem compounded by the cybersecurity skills gap. Attackers know this and often generate “noise” (decoy attacks) to hide their actual exfiltration activities.
2. Contextualization: How Machine Learning Connects the Dots
Next-generation SIEMs (like Microsoft Sentinel, Splunk AI, or Google SecOps) use machine learning to move from Rule-Based Detection to Context-Based Detection.
Instead of treating every log entry as an isolated event, the AI groups related alerts into a single Incident.
- The Attack Chain: The AI sees a phishing email blocked (Email Gateway log), followed by a successful login from an unusual IP (Identity log), followed by a PowerShell execution (EDR log).
- The Correlation: A legacy SIEM generates three separate alerts of “Low” or “Medium” severity that different analysts might review at different times. An AI-powered SIEM correlates these logs mathematically, recognizing the pattern of a coordinated attack, and generates one “Critical” incident timeline.
3. Automated Triage and Risk Scoring
AI dramatically reduces the analyst’s workload through automated triage. When an incident is generated, the AI immediately goes to work before a human ever sees the screen:
- Enrichment: The AI queries external Threat Intelligence feeds (like VirusTotal or AlienVault) to see if the IP address or file hash is known to be malicious.
- Historical Analysis: It checks if this specific alert pattern has happened before and how previous analysts resolved it (e.g., “Was this marked as a false positive last week?”).
- Dynamic Prioritization: Based on the asset’s value (e.g., a CEO’s laptop vs. a guest Wi-Fi router) and the confidence of the ML model, the AI assigns a risk score. It pushes critical threats to the top of the queue and auto-closes or suppresses benign anomalies.
4. Generative AI in the SOC: Natural Language Threat Hunting
The most recent and revolutionary addition to the SIEM is the integration of Large Language Models (LLMs) tuned specifically for cybersecurity.
Historically, Threat Hunting required deep knowledge of complex query languages (like KQL for Microsoft or SPL for Splunk). Today, an analyst can use natural language prompts.
- The Prompt: “Show me all users who logged in from outside the EU in the last 24 hours and subsequently accessed the financial database.”
- The Execution: The AI translates this English sentence into the correct database query, executes it, and summarizes the findings in a readable report, complete with recommendations for remediation.
Conclusion
AI is not replacing the SOC analyst; it is replacing the tedious, repetitive data-gathering tasks that lead to burnout. By automating correlation, triage, and query generation, AI-powered SIEMs allow analysts to focus on what humans still do best: critical thinking, complex problem-solving, and strategic incident response.
Next week, we will look at the logical next step: once the SIEM identifies the threat, how do we use AI to automatically stop it in real-time? We will dive into the world of SOAR (Security Orchestration, Automation, and Response).
