Cloud Security Posture Management (CSPM): AI for Config Monitoring
Discover how Artificial Intelligence is transforming CSPM, moving cloud security from noisy, static alerts to contextual, auto-remediated posture management.
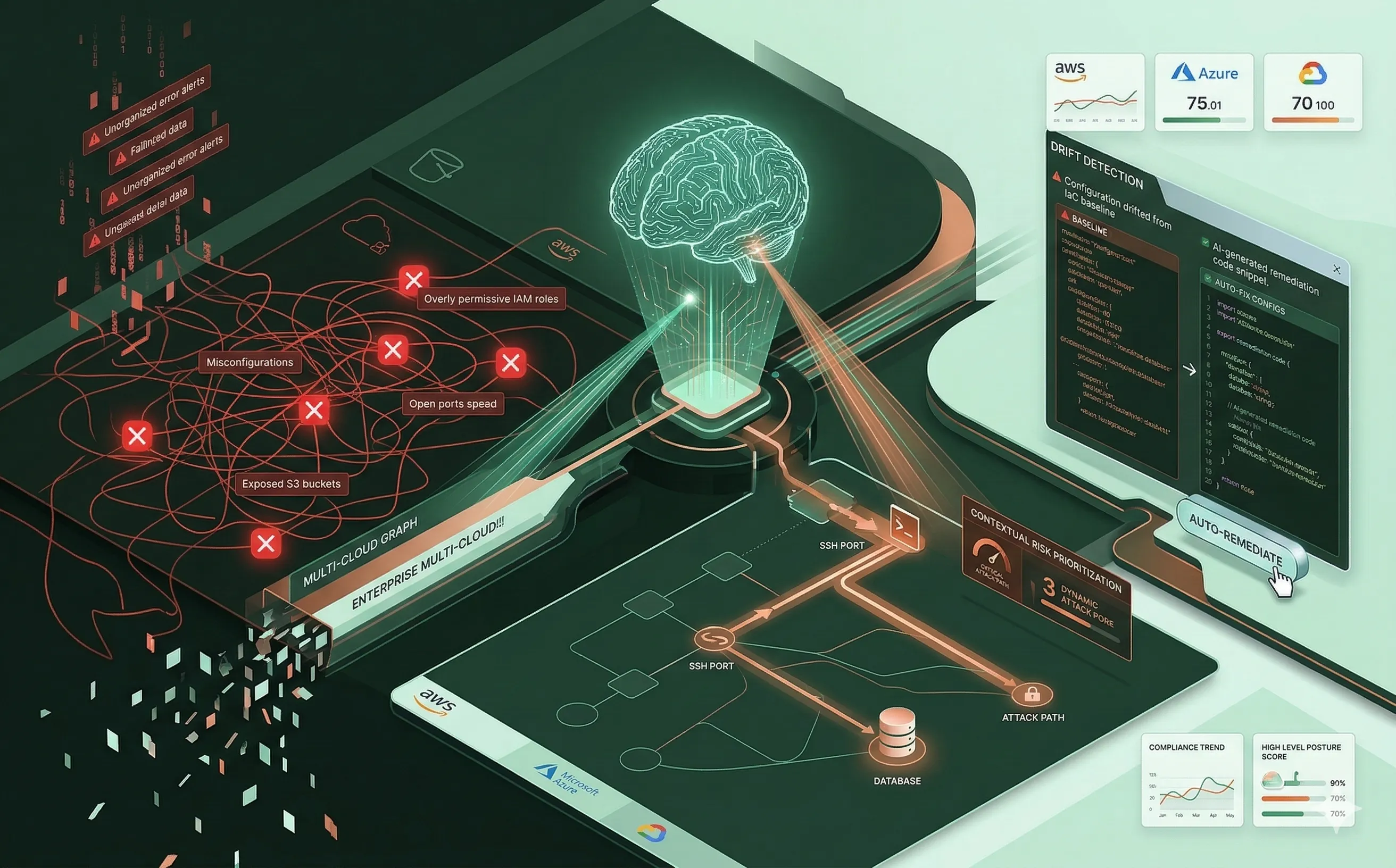
Introduction: The Misconfiguration Epidemic
As enterprises finalize their migrations to the cloud, IT leaders are discovering a painful reality: the cloud is secure by design, but it is rarely secure by default. The vast majority of cloud data breaches are not the result of sophisticated zero-day exploits or quantum decryption; they are caused by simple, human-generated misconfigurations. An overly permissive IAM role, an exposed AWS S3 bucket, or a misconfigured Azure Network Security Group is all an attacker needs to compromise an entire infrastructure — especially in organizations that lack a robust Zero Trust architecture.
To combat this, the industry adopted Cloud Security Posture Management (CSPM) tools to continuously scan environments for misconfigurations. However, as organizations embrace multi-cloud architectures, traditional CSPMs have become overwhelmed, drowning security teams in thousands of static, context-less alerts. To restore visibility and govern these sprawling environments effectively, IT architects are now integrating Artificial Intelligence into CSPM, shifting from reactive alerting to predictive, context-aware posture management.
1. The Multi-Cloud Visibility Crisis
The fundamental challenge of modern cloud governance is scale. A typical enterprise uses a combination of AWS, Microsoft Azure, and Google Cloud Platform (GCP). Each of these providers offers hundreds of unique services, each with its own complex, deeply nested configuration and Identity and Access Management (IAM) syntax.
- Ephemeral Infrastructure: In a DevSecOps environment, infrastructure is defined as code (IaC) and is highly ephemeral. Virtual machines and containers are spun up and destroyed in minutes. Human auditors cannot physically keep pace with this rate of change.
- Alert Fatigue: Legacy CSPM tools operate on rigid, binary rules (e.g., “Alert if an SSH port is open to the internet”). In a massive enterprise, this rule might trigger 5,000 times a day. If security analysts have to manually investigate every alert, “Alert Fatigue” sets in, and critical vulnerabilities are inevitably ignored.
2. From Static Rules to ML-Driven Context
Artificial Intelligence transforms CSPM by introducing Contextual Risk Analysis. Instead of looking at individual misconfigurations in isolation, machine learning models analyze the entire cloud environment as an interconnected graph.
- Attack Path Mapping: An AI-enhanced CSPM understands the relationships between assets. It evaluates an open port not as a binary failure, but by tracing its potential impact. If an EC2 instance has an open port and possesses an IAM role with read access to a customer database and the database contains unencrypted PII, the AI correlates these disparate facts.
- Prioritization: By understanding the actual attack path, the AI dynamically scores the risk. It suppresses the 4,999 open ports attached to empty, isolated test servers, and escalates the single open port that leads directly to critical business data, allowing the security team to focus strictly on existential threats.
3. Auto-Remediation and Infrastructure as Code (IaC)
Detecting a misconfiguration is only half the battle; fixing it without breaking production is the true managerial challenge. AI is bridging this gap by enabling intelligent Auto-Remediation.
- Drift Detection: When an engineer manually changes a setting in the AWS console to troubleshoot an issue, the environment “drifts” from its approved Infrastructure as Code (IaC) baseline. The AI-driven CSPM instantly detects this drift.
- Automated Pull Requests: Advanced CSPMs use Large Language Models (LLMs) trained on Terraform, AWS CloudFormation, and Pulumi syntaxes. When a vulnerability is found, the AI does not just send a slack message; it automatically generates the exact code required to fix the flaw and submits a Pull Request directly to the developer’s Git repository. The developer simply reviews the AI’s code and clicks “Merge,” remediating the cloud infrastructure in minutes.
4. Strategic Governance and Continuous Compliance
For IT managers and Chief Information Security Officers (CISOs), CSPM is ultimately a governance tool. Organizations are subject to strict regulatory frameworks—such as GDPR, HIPAA, SOC 2, and the ISO 27000 series—that mandate specific technical controls.
- Automated Auditing: AI-powered CSPMs continuously map the real-time configuration of the multi-cloud environment directly against these legal frameworks. If an engineer deploys a database without at-rest encryption, the CSPM flags it not just as a security risk, but as an immediate compliance violation.
- Executive Reporting: Machine learning models synthesize millions of data points into high-level posture scores and trend lines. This allows IT leadership to track the organization’s security posture over time, prove continuous compliance to external auditors, and justify security budgets to the board of directors.
Conclusion
The era of managing cloud security via manual audits and static spreadsheets is over. The complexity and velocity of multi-cloud environments demand a strategic, automated approach. By leveraging AI-driven Cloud Security Posture Management, IT leaders can cut through the noise of alert fatigue, automatically remediate configuration drift, and ensure their sprawling infrastructure remains secure, compliant, and continuously governed. When combined with an AI-powered SIEM, these tools form a comprehensive security operations backbone.
