IoT Security: Protecting Smart Devices with Lightweight Models
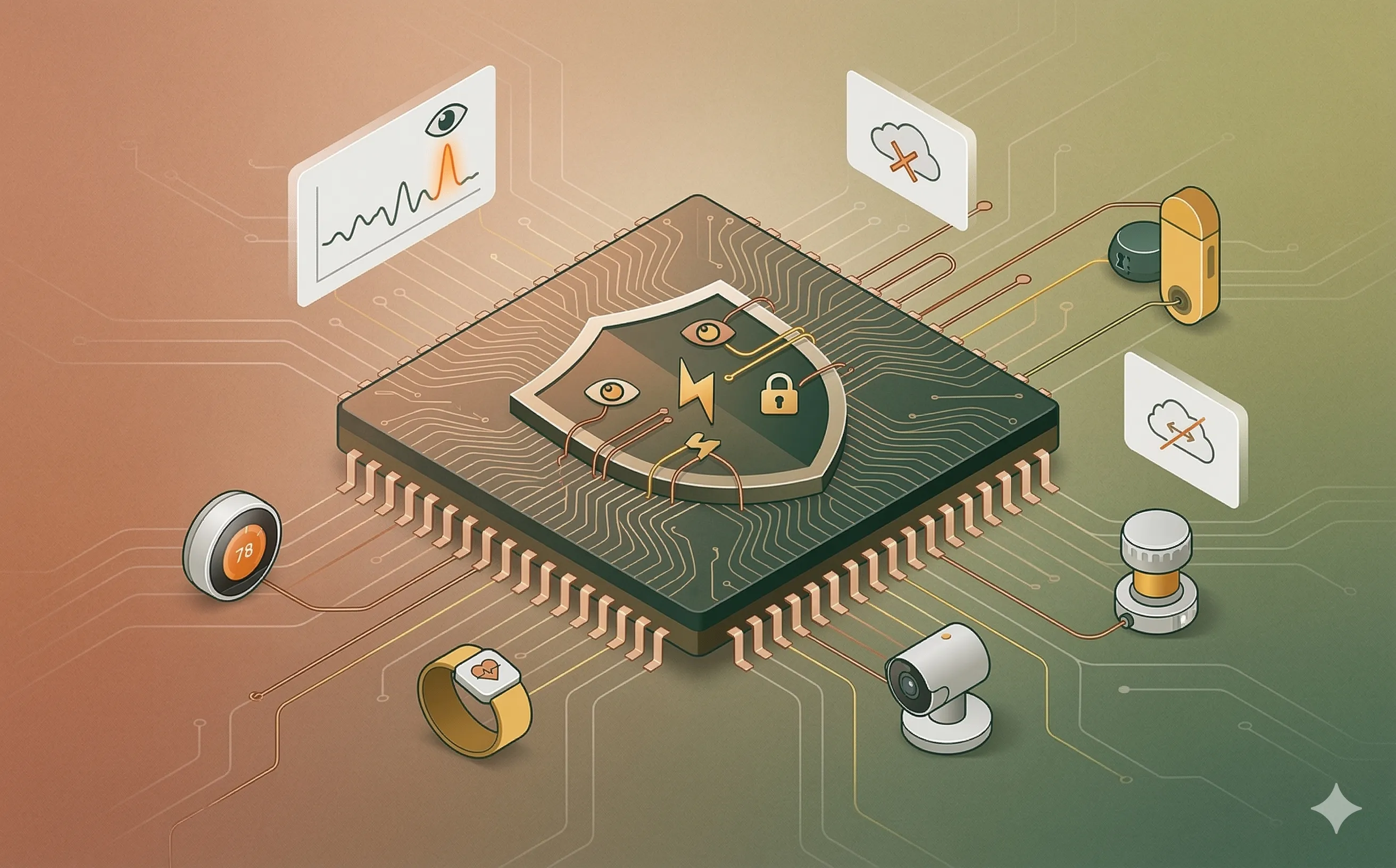
Discover how TinyML and lightweight machine learning models are securing the Internet of Things, bringing real-time anomaly detection to resource-constrained edge devices.
Introduction: The Unsecured Edge
The Internet of Things (IoT) has fundamentally transformed enterprise architecture. From industrial sensors monitoring factory floor vibrations to smart medical wearables tracking patient vitals, IoT devices bridge the physical and digital worlds. However, this massive proliferation of connected devices has created an infinitely expanding attack surface.
The fundamental problem with IoT security is hardware capability. Traditional cybersecurity relies on heavy software agents — Endpoint Detection and Response (EDR) tools, continuous cloud telemetry, and complex encryption protocols. You simply cannot run a traditional EDR agent on a smart thermostat that operates on a few kilobytes of RAM and a watch battery. Attackers exploit this vulnerability daily, recruiting unsecured IoT devices into massive botnets or using them as unmonitored entry points for lateral movement into corporate networks. To secure the edge, IT leaders are pivoting to a new paradigm: TinyML and Lightweight Machine Learning Models.
1. The Resource-Constraint Paradox
To understand the strategic shift toward lightweight models, IT architects must first understand the severe engineering constraints of the IoT ecosystem.
- Compute and Memory Limits: A typical microcontroller (MCU) running an IoT device possesses tens to hundreds of kilobytes (KB) of RAM and relies on processors operating in the megahertz (MHz) range. They lack the Graphical Processing Units (GPUs) required for traditional AI.
- Power Budgets: Many IoT devices are deployed in remote or industrial environments where they must run for years on a single battery or via energy harvesting. Sending constant streams of telemetry data to a cloud SIEM (Security Information and Event Management) system consumes catastrophic amounts of power via the radio transmitter.
- The Security Gap: Because IoT devices cannot support heavy security agents or continuous cloud communication, they are effectively “blind” to sophisticated attacks like zero-day exploits or stealthy data exfiltration until the compromise is detected at the network traffic analysis level — which is often too late.
2. TinyML: Security at the Silicon Level
The solution to the resource-constraint paradox is Tiny Machine Learning (TinyML). TinyML is a subset of Edge AI that focuses on deploying highly optimized, miniature machine learning models directly onto microcontrollers.
Instead of relying on massive, power-hungry Deep Neural Networks hosted in the cloud, DevSecOps teams use lightweight algorithms such as Decision Trees, k-Nearest Neighbors (KNN), Support Vector Machines (SVM), and highly quantized Convolutional Neural Networks (CNNs).
To make these models fit on an MCU, engineers employ two primary techniques:
- Quantization: Reducing the precision of the model’s mathematical weights (e.g., converting 32-bit floating-point numbers to 8-bit integers). This drastically shrinks the model’s memory footprint with minimal loss in accuracy.
- Pruning: Mathematically removing the “dead” or less important neural connections within the model, reducing the computational cycles required to make a decision.
3. On-Device Anomaly Detection and Intrusion Prevention
By embedding lightweight models directly into the firmware, the IoT device becomes self-aware and capable of autonomous defense without needing cloud connectivity.
- Behavioral Baselining: A TinyML model can be trained to understand the “normal” operating rhythm of the device. It monitors local hardware telemetry: CPU utilization, memory allocation, power consumption spikes, and the cadence of network packet transmission.
- Real-Time Intrusion Detection: If an attacker attempts a memory corruption exploit or tries to install a crypto-miner on a smart security camera, the device’s behavior instantly deviates from its baseline. The lightweight model detects this anomaly in milliseconds.
- Autonomous Isolation: Because the intelligence is processed locally, the device can take immediate action. If a smart industrial valve detects anomalous network behavior indicating a potential ransomware attack, the TinyML model can trigger a local hardware interrupt, shutting down its network interface while maintaining its critical physical functions.
4. Strategic Advantages: Privacy, Latency, and Cost
For technology managers and IT strategists, adopting lightweight models for IoT security is not just a technical upgrade; it solves several broader business and compliance challenges.
- Data Privacy and GDPR Compliance: By processing security analytics directly on the device, raw data (such as audio from a smart speaker or video from a camera) never has to be transmitted to a third-party cloud server for threat analysis. This “data minimization” inherently strengthens compliance with strict privacy frameworks like the GDPR.
- Ultra-Low Latency: In Industrial IoT (IIoT) environments, a delayed security response can result in physical damage or human injury. Localized models guarantee millisecond reaction times, completely immune to internet outages or cloud server downtime.
- Reduced Cloud Expenditures: Transmitting millions of raw security logs from thousands of edge devices to a centralized cloud incurs massive bandwidth and storage costs. TinyML filters the noise at the edge, only alerting the central SIEM when a high-confidence threat is detected, significantly optimizing IT budgets.
Conclusion
The era of treating IoT devices as “dumb” endpoints that must be protected by external firewalls is ending. The hardware limitations of the edge require an entirely new approach to cybersecurity. By integrating TinyML and lightweight machine learning models into the development lifecycle, organizations can embed autonomous, intelligent security directly into the silicon of their smart devices, effectively neutralizing one of the most vulnerable attack vectors in modern enterprise architecture.
