Network Traffic Analysis (NTA): Detecting Encrypted Malicious Traffic
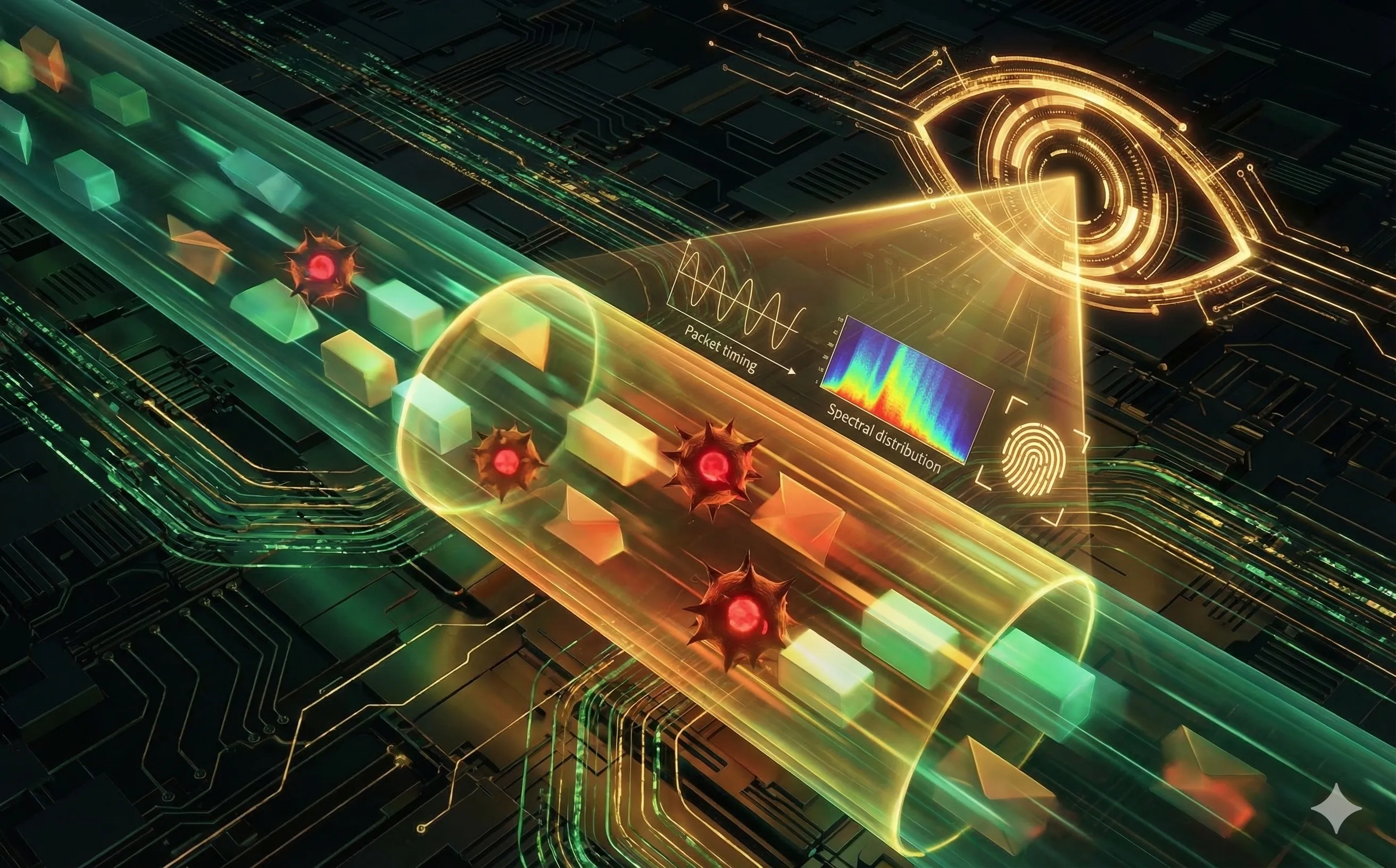
Learn how AI-powered Network Traffic Analysis (NTA) detects malware and data exfiltration hidden inside encrypted HTTPS and TLS traffic without decrypting it.
Introduction: The Double-Edged Sword of Encryption
Today, over 80% of all internet traffic is encrypted using protocols like TLS and HTTPS. From a user privacy perspective, this is a massive victory. However, from a Blue Team perspective, it is a nightmare.
Malware authors, ransomware operators, and insider threats now routinely use the exact same encryption protocols as legitimate banking websites to hide their communications. Traditional security tools are effectively blind to this traffic. Network Traffic Analysis (NTA) powered by Machine Learning is the industry’s answer: a way to detect the malicious intent inside the tunnel without ever breaking the encryption.
1. The Death of Deep Packet Inspection (DPI)
Historically, firewalls and Intrusion Detection Systems (IDS) relied on Deep Packet Inspection (DPI). They would open up the network packet, read the payload, and look for malicious signatures.
With the rise of TLS 1.3, reading the payload is mathematically impossible without the decryption keys. For a while, enterprises bypassed this using “SSL Decryption” (acting as a sanctioned Man-in-the-Middle by intercepting traffic, decrypting it, inspecting it, and re-encrypting it). However, this approach is highly resource-intensive, raises massive data privacy concerns, and frequently breaks modern applications that use certificate pinning. A new approach was needed: one that analyzes the behavior of the traffic rather than its content.
2. Machine Learning and Metadata Analysis
If you cannot read the letter inside the envelope, you must analyze the envelope itself. AI-driven NTA models ingest millions of data points of network metadata—the observable characteristics of the encrypted flow.
- Packet Size and Timing: A user watching a YouTube video generates a steady stream of large packets flowing in one direction. A compromised server participating in a botnet DDoS attack generates thousands of tiny packets in milliseconds.
- Byte Distribution: The mathematical entropy of the encrypted payload can reveal what type of file is inside. An AI can learn the subtle statistical differences between an encrypted PDF being downloaded versus an encrypted executable (
.exe) being smuggled onto a machine. - Flow Duration: How long does the connection stay open? A normal web browsing session is bursty. A persistent, low-volume connection held open for 48 hours is highly indicative of a reverse shell.
3. Fingerprinting the TLS Handshake
Before encryption actually begins, the client and the server must negotiate the rules of the secure tunnel. This is called the TLS Handshake, and it is largely sent in plaintext.
NTA platforms use algorithms like JA3 / JA4 to fingerprint the client application based on how it negotiates this handshake (e.g., the specific order of ciphers and extensions it offers).
- A legitimate Google Chrome browser negotiates TLS in a very specific, recognizable way.
- A custom Python script used by a malware operator to exfiltrate data negotiates TLS differently. Even if the subsequent traffic is perfectly encrypted, the AI recognizes the malicious “fingerprint” from the initial handshake and blocks the connection.
4. Detecting C2 Beaconing and Exfiltration
Advanced Persistent Threats (APTs) rely on Command and Control (C2) servers to send instructions to compromised endpoints. To avoid detection, the malware “beacons” out—sending a tiny, encrypted ping to the C2 server every few hours to ask, “Do you have any new commands for me?”
- Beacon Detection: These beacons use “jitter” (randomized delays) to avoid triggering static firewall rules. However, unsupervised machine learning algorithms excel at finding hidden periodic rhythms in massive datasets. The NTA model detects the underlying mathematical pattern of the beacon, even if the timing is randomized and the payload is encrypted.
- Slow Exfiltration: If an attacker tries to download a 50GB database in 10 minutes, standard alarms will sound. So, attackers use “low and slow” exfiltration, leaking a few megabytes of encrypted data per day. NTA models baseline the normal outbound data transfer rate for every specific server. When the AI detects a slow, consistent deviation from that baseline over several weeks, it flags the stealth exfiltration.
Conclusion
You no longer need to see the data to know it is dangerous. By shifting the focus from payload inspection to behavioral metadata analysis, AI-driven NTA restores visibility to the Blue Team. It proves that even when attackers wrap their communications in military-grade cryptography, their automated behaviors still leave a detectable, mathematical footprint on the network.
