Predictive Threat Intelligence: Forecasting Attacks Before They Happen
Discover how AI transforms Threat Intelligence from reactive blacklists into predictive models that forecast cyberattacks before they happen.
Introduction: The Minority Report of Cybersecurity
In our previous articles, we optimized the SOC to detect anomalies (UEBA) and respond at machine speed (SOAR). However, even a response time of three seconds means the attacker has already knocked on your door or breached your perimeter.
What if you could block the attacker before they even launched the campaign?
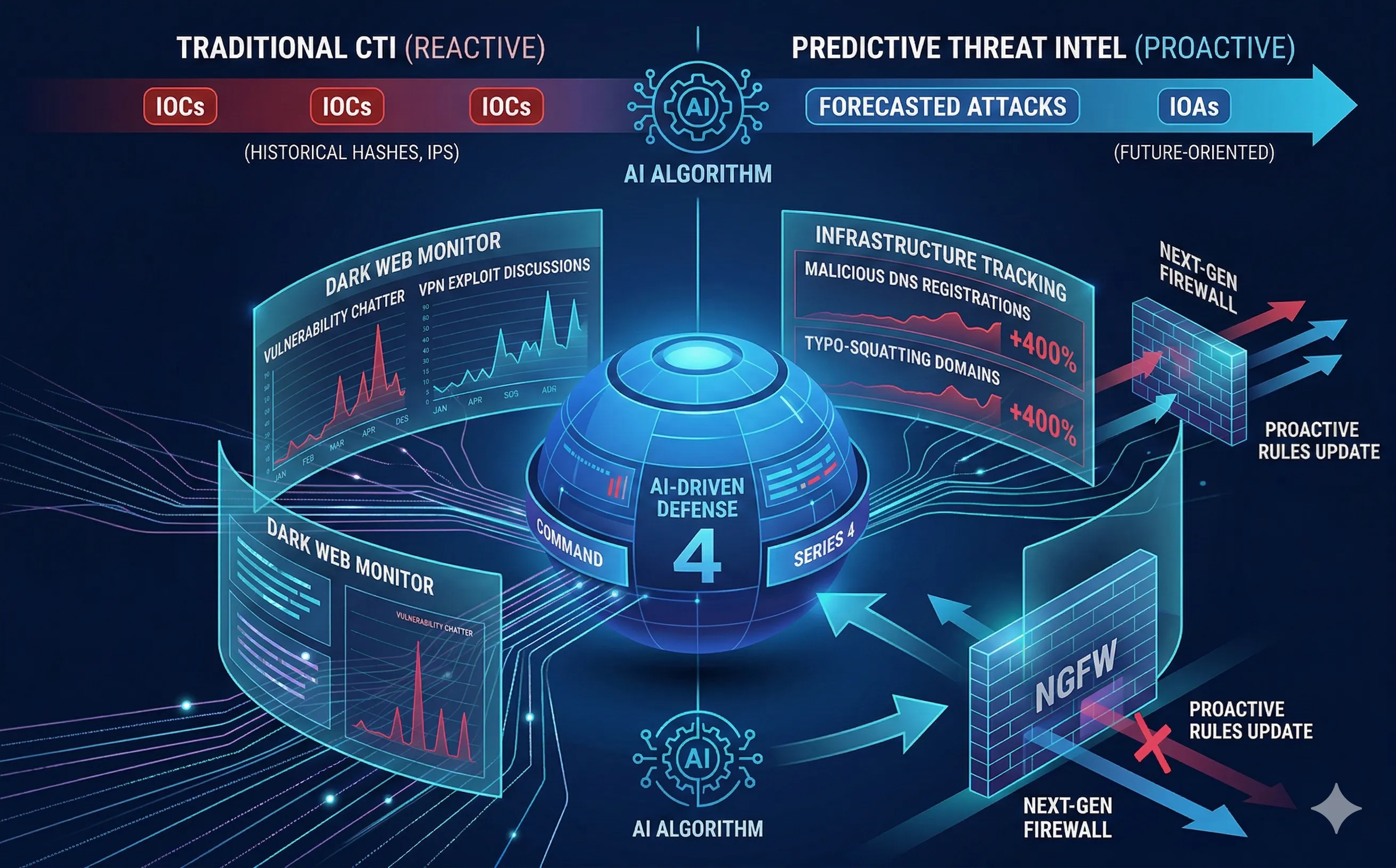
This is the promise of Predictive Threat Intelligence. By applying Machine Learning to global datasets, the cybersecurity industry is moving away from purely historical data (reacting to yesterday’s attacks) toward forecasting (predicting tomorrow’s targets). We are transitioning from a reactive posture to a truly proactive defense.
1. The Limitation of Traditional CTI
Traditional Cyber Threat Intelligence (CTI) relies heavily on Indicators of Compromise (IOCs)—things like malicious IP addresses, known bad file hashes, and compromised domains.
The fundamental flaw with IOCs is that they are inherently historical. By the time a malicious IP is added to a global blacklist and downloaded to your firewall, that IP has already been used to attack someone else. Furthermore, with the rise of AI-driven polymorphic malware and disposable cloud infrastructure, attackers change their IPs and file hashes for every single victim. A blacklist is essentially a list of bullets that have already been fired.
2. How Predictive AI Analyzes the “Pre-Attack” Phase
Predictive AI shifts the focus from Indicators of Compromise to Indicators of Attack (IOAs) and behavioral forecasting. It achieves this by ingesting and analyzing colossal amounts of unstructured data from the deep and dark web using Natural Language Processing (NLP) and OSINT techniques.
- Dark Web Chatter Analysis: AI models continuously scrape hacker forums, Telegram channels, and illicit marketplaces. If the NLP detects a sudden 400% spike in conversations about a specific, unpatched VPN vulnerability (even if an exploit script isn’t public yet), the AI flags this as an impending wave of attacks.
- Infrastructure Tracking: Attackers have to build infrastructure before launching a campaign. Machine Learning algorithms monitor global DNS registrations and server provisioning. If an AI detects that a known threat actor group (like APT29) is suddenly registering hundreds of domains that look vaguely like Microsoft login pages, it predicts a massive phishing campaign is imminent.
3. Real-World Applications in the Enterprise
How does a SOC actually use this predictive capability?
- Vulnerability Prioritization: An enterprise might have 10,000 unpatched vulnerabilities. Patching them all immediately is impossible. Predictive AI analyzes the global threat landscape to score vulnerabilities not just by their CVSS score, but by their probability of exploitation. It tells the IT team: “Ignore the critical server flaw for today; patch this medium-severity firewall bug immediately, because AI predicts it will be weaponized in the next 48 hours.”
- Pre-emptive Domain Blocking: Predictive algorithms can analyze a company’s domain name (e.g.,
company.com) and generate thousands of probable typo-squatted variations (c0mpany.com,compnay.com). The system can then automatically feed these predicted domains into the corporate proxy to block them proactively, neutralizing future phishing links before they are even registered by an attacker.
4. Integrating the Ecosystem
Predictive Threat Intelligence is not a standalone tool; it is the “fuel” that powers the rest of the defense architecture.
When a predictive model forecasts that a specific IP range belonging to a bulletproof hosting provider is being prepped for a botnet attack, it automatically pushes those IPs via API to the enterprise’s SIEM, Next-Generation Firewalls (NGFW) and Web Application Firewalls (WAF). When the attack actually begins three days later, the enterprise’s infrastructure drops the packets instantly, because the AI already updated the access control lists.
Conclusion
Cybersecurity is fundamentally an asymmetric war: the attacker only needs to be right once, while the defender must be right every time. Predictive Threat Intelligence uses AI to tilt the scales back in favor of the defender. By understanding the adversary’s logistics, supply chains, and communication patterns, organizations can shift from putting out fires to removing the oxygen before the spark is even lit.
