Quantum Computing: The Threat to Current Encryption
Understand the looming threat of quantum computing on modern cryptography. Explore the 'Harvest Now, Decrypt Later' risk and the strategic transition to Post-Quantum Cryptography (PQC).
Introduction: The Existential Threat to Trust
While Artificial Intelligence dominates today’s technology watch, IT strategists must simultaneously prepare for the next paradigm shift: Quantum Computing. Unlike classical computers that process bits (0s and 1s), quantum computers use qubits, allowing them to exist in multiple states simultaneously and solve specific complex mathematical problems exponentially faster.
For the cybersecurity industry, this is not just a hardware evolution; it is an existential threat. The entire foundation of digital trust—secure web browsing, VPNs, digital signatures, and secure communications—relies on public-key cryptography. Within the next decade, a sufficiently powerful quantum computer will be able to shatter these cryptographic foundations, creating a hypothetical event the industry calls “Q-Day.” For IT managers and enterprise architects, the preparation for Q-Day must begin today.
1. Shor’s Algorithm and the Vulnerability of RSA
To understand the threat, we must understand how modern encryption works. Asymmetric encryption protocols, such as RSA and Elliptic Curve Cryptography (ECC), secure data across the internet. Their security relies entirely on the mathematical difficulty of factoring massively large prime numbers or solving discrete logarithms. A classical supercomputer would take millions of years to crack a 2048-bit RSA key.
However, in 1994, mathematician Peter Shor developed Shor’s Algorithm.
- The Quantum Advantage: Shor’s algorithm proves that a cryptographically relevant quantum computer (CRQC) can factor these large primes in hours or even minutes.
- The Impact: When a CRQC becomes viable, all data secured by RSA, Diffie-Hellman, and ECC will instantly become transparent.
(Note: Symmetric encryption like AES-256 is targeted by a different quantum formula called Grover’s Algorithm, which halves the effective key size. However, AES-256 remains largely quantum-resistant, meaning asymmetric public-key cryptography is the primary emergency).
2. The Strategic Danger: “Harvest Now, Decrypt Later”
A common managerial pushback is: “If quantum computers capable of breaking RSA won’t exist for another 5 to 10 years, why should we invest in mitigating the threat today?”
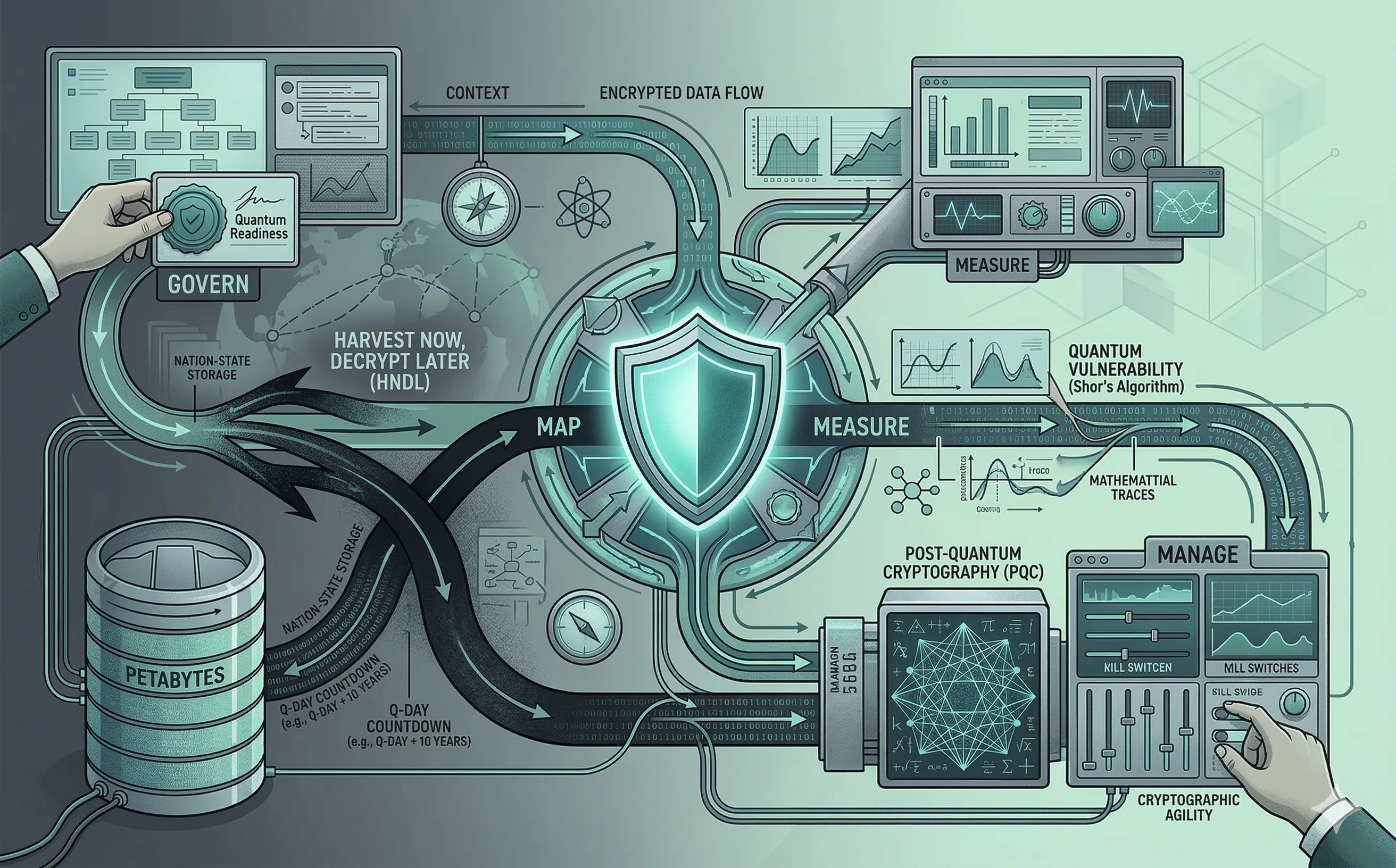
The answer lies in a highly aggressive, ongoing intelligence strategy known as Harvest Now, Decrypt Later (HNDL) or Store Now, Decrypt Later (SNDL). Nation-state threat actors are currently intercepting and exfiltrating massive volumes of encrypted enterprise and government data through sophisticated network traffic analysis and interception techniques. They know they cannot read the AES keys wrapped in RSA today. However, they are storing these petabytes of encrypted data in massive data centers. As soon as they achieve quantum capability, they will retrospectively decrypt the stored data.
If your organization handles data with a long-term secrecy requirement—such as healthcare records, proprietary source code, national security intelligence, or long-term financial strategies—your data is already actively compromised by the HNDL threat vector.
3. The Solution: Post-Quantum Cryptography (PQC)
The IT industry is not waiting for Q-Day to happen. For years, the National Institute of Standards and Technology (NIST) has been leading a global effort to evaluate and standardize new cryptographic algorithms that are mathematically resistant to both classical and quantum attacks.
This new generation of algorithms is known as Post-Quantum Cryptography (PQC).
- Math Over Physics: Unlike Quantum Key Distribution (QKD), which requires specialized physical hardware and fiber optics, PQC relies on entirely new branches of mathematics (such as lattice-based cryptography).
- New Standards: NIST has already begun finalizing the first official PQC standards (like ML-KEM for key encapsulation and ML-DSA for digital signatures). These algorithms are designed to be deployed on current, classical hardware, replacing RSA and ECC via software updates.
4. The Managerial Imperative: Cryptographic Agility
Transitioning an entire enterprise architecture from RSA to PQC will be the largest cybersecurity migration in history, dwarfing the Y2K transition. IT leaders must initiate this transition immediately by establishing Cryptographic Agility.
Organizations must adopt a governance framework to manage this migration:
- Create a Cryptographic Bill of Materials (CBOM): You cannot upgrade what you cannot see. IT teams must audit their entire software supply chain to discover exactly where and how cryptography is being used. Which microservices hardcode RSA? Which legacy applications rely on outdated TLS versions?
- Eliminate Hardcoded Cryptography: Developers must stop hardcoding specific cryptographic algorithms into application logic. Security architectures should abstract cryptography into centralized key management systems or sidecars, allowing the organization to swap an RSA certificate for a PQC certificate with a simple configuration change, rather than a massive codebase rewrite.
- Hybrid Implementations: In the short term, security architects should adopt hybrid cryptographic models. This involves wrapping data in both a traditional algorithm (like ECC) and a new PQC algorithm simultaneously. This guarantees compliance with current FIPS standards while providing early protection against the HNDL threat.
Conclusion
Quantum computing is a slow-moving but unavoidable tidal wave. For technology leaders and professionals outlining long-term IT strategies, ignoring the quantum threat is a failure of governance. By understanding the “Harvest Now, Decrypt Later” paradigm and beginning the complex migration toward Post-Quantum Cryptography and Cryptographic Agility, organizations can ensure their data remains secure in a post-RSA world.
