SAST vs. DAST: Enhancing Code Scanning with Machine Learning
Explore how Machine Learning is transforming SAST and DAST, reducing false positives, and detecting complex vulnerabilities in modern applications.
Introduction: The Application Security Bottleneck
For years, the foundation of Application Security (AppSec) has rested on two primary testing methodologies: Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST). SAST analyzes the source code from the inside out before the application runs, while DAST attacks the running application from the outside in.
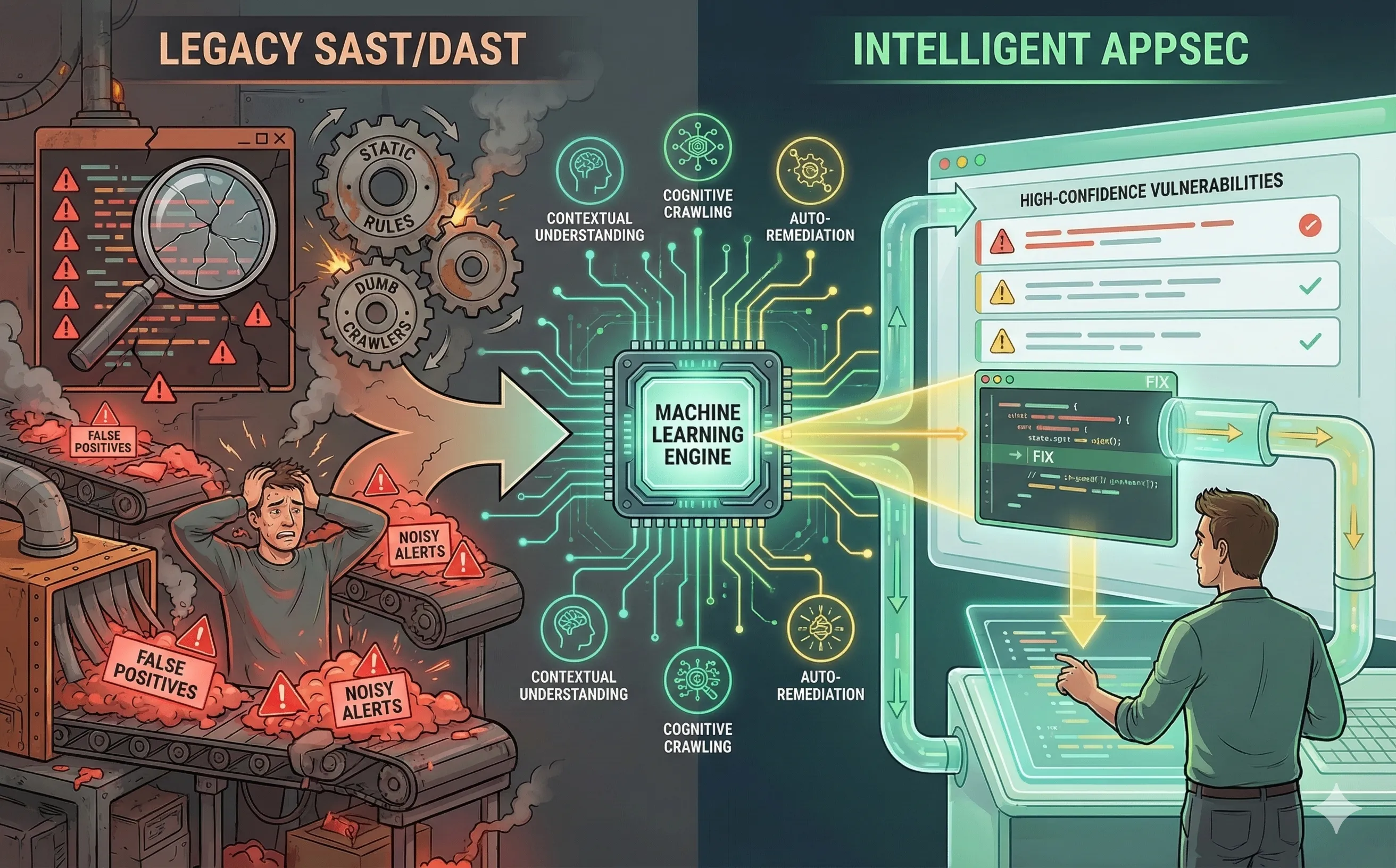
Together, they are supposed to provide comprehensive coverage. However, in modern CI/CD pipelines where developers deploy code multiple times a day, legacy SAST and DAST tools have become massive bottlenecks. They are notoriously noisy, slow, and rigid. To keep up with the speed of Agile development, the AppSec industry is injecting Machine Learning (ML) into these traditional scanners, transforming them from rigid rule-engines into intelligent, context-aware security analysts.
1. The Legacy SAST Problem: Noise and Alert Fatigue
Traditional SAST tools operate using strict, regex-based rule sets. If a rule says, “Flag any instance where user input is concatenated into a SQL query,” the scanner will blindly flag it.
While this catches obvious SQL injections, it completely ignores context. If the developer already sanitized that input three functions earlier using a custom library, the legacy SAST doesn’t know. It still throws a “Critical” alert. This results in massive false-positive rates—often upwards of 70%. When developers are forced to manually triage hundreds of fake alerts to find one real vulnerability, trust in the security tooling plummets, and “Alert Fatigue” sets in.
2. How ML Transforms SAST: Contextual Understanding
Machine Learning fundamentally changes how SAST operates. Instead of just matching string patterns, ML models are trained on millions of open-source and proprietary codebases to understand the data flow and the semantic context of the code.
- False Positive Reduction: When an ML-enhanced SAST finds a potential vulnerability, it traces the execution path. It recognizes custom sanitization functions and contextual safety measures that a rigid regex rule would miss. By mathematically calculating the probability of a finding being a true positive, it automatically suppresses the noise, presenting only high-confidence alerts to the developer.
- Auto-Remediation: Advanced ML models don’t just point out the broken code; they generate the exact block of code needed to fix it. If the scanner detects an insecure cryptographic cipher, the ML engine will suggest a pull request replacing it with an AES-GCM implementation that seamlessly integrates into the surrounding logic. This kind of intelligent remediation pairs well with secure coding practices in AI-assisted development.
3. The Legacy DAST Problem: Crawling Modern Web Apps
DAST tools mimic a human attacker interacting with a live web application. Historically, DAST “spiders” or crawlers navigate a site by clicking standard HTML <a href> links and submitting <form> tags.
This approach fails completely on modern Single Page Applications (SPAs) built with React, Angular, or Vue. In SPAs, the page never actually reloads; navigation is handled dynamically via JavaScript, and data is fetched via complex, undocumented REST or GraphQL APIs. A legacy DAST crawler looks at a React application, sees only a single index.html file, and assumes the site is empty, completely missing the massive attack surface hidden behind the JavaScript.
4. How AI Upgrades DAST: Intelligent Crawling and Fuzzing
To audit modern architectures, DAST must act more like a cognitive entity than a simple web scraper. Artificial Intelligence bridges this gap by enabling intelligent navigation and dynamic payload generation.
- Cognitive Crawling: Machine Learning models equipped with computer vision and natural language processing can “see” the application like a human. They understand that a visually rendered button labeled “Submit” is an actionable element, even if it lacks traditional HTML form tags. The AI maps the complex state changes of the SPA, uncovering hidden API endpoints that standard crawlers miss.
- Smart Payload Generation: Instead of blindly throwing a static dictionary of SQL injection payloads at an input field, ML-driven DAST analyzes the API’s response behavior. If the server responds with a specific database error, the AI dynamically adapts its next set of payloads (similar to automated fuzzing at scale) to actively exploit the specific backend technology it has inferred, discovering complex, multi-step vulnerabilities that static lists cannot reach.
Conclusion
The friction between security and development teams often stems from bad tooling. Developers want to ship fast; security wants to ship safely. By upgrading SAST and DAST with Machine Learning, DevSecOps teams can drastically reduce the noise of false positives and increase the coverage of modern architectures. The result is a security pipeline that operates at the speed of code, acting as an enabler rather than a roadblock.
