Self-Healing Networks: AI-Driven Patch Management
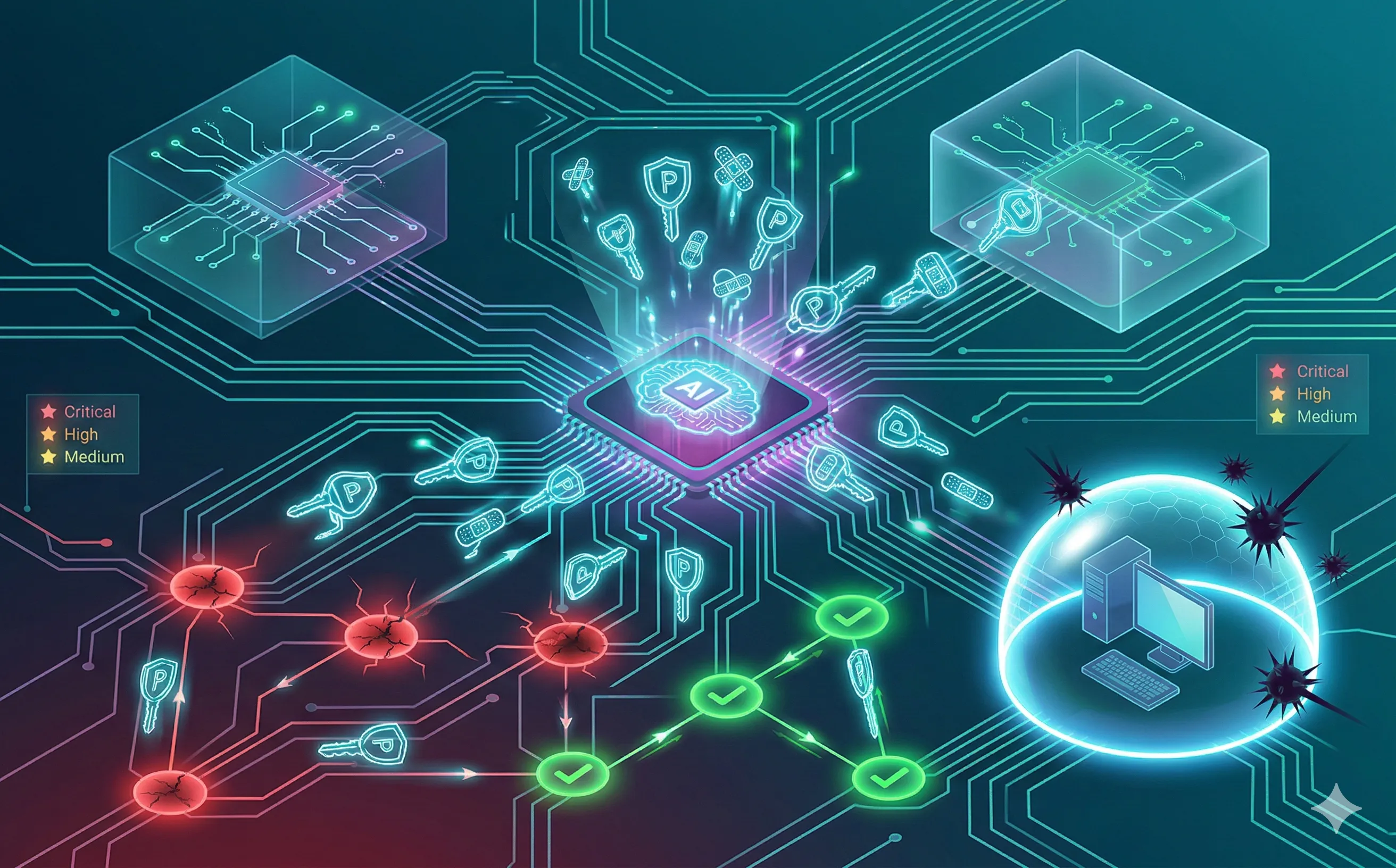
Discover how AI-driven self-healing networks automate patch management, prioritize vulnerabilities, and dynamically isolate unpatched systems.
Introduction: The Vulnerability Backlog Crisis
One of the oldest and most persistent problems in IT security is not advanced nation-state malware; it is unpatched software. The National Vulnerability Database (NVD) registers tens of thousands of new Common Vulnerabilities and Exposures (CVEs) every year. For a system administrator managing thousands of endpoints and servers, the sheer volume creates an impossible backlog.
The Mean Time To Patch (MTTP) for a typical enterprise is often measured in weeks or months, while attackers weaponize known vulnerabilities (N-days) in a matter of days. This gap is where ransomware thrives. To close it, the industry is moving towards Self-Healing Networks, leveraging Artificial Intelligence (AIOps) to transform patch management from a manual, terrifying chore into an autonomous, continuous process.
1. The Problem with Manual Patching
Why do IT teams delay patching? Fear of breaking production.
Historically, deploying a critical Windows or Linux patch required a maintenance window, manual testing in a staging environment, and the crossing of fingers. A bad patch can cause the “Blue Screen of Death” (BSOD) on thousands of machines, paralyzing the business faster than an actual cyberattack. Because the risk of disruption is so high, patching is delayed, leaving the door wide open for attackers exploiting known flaws like ProxyLogon or PrintNightmare.
2. Context-Aware Prioritization
The first step in a self-healing architecture is knowing what to heal first. Legacy scanners treat every “Critical” (CVSS 10) vulnerability equally. AI-driven Risk-Based Vulnerability Management (RBVM) adds business context.
The AI analyzes the entire network topology and asks:
- Is this vulnerable server actually exposed to the public internet?
- Does this database contain sensitive customer data?
- Are there active exploit kits for this CVE currently being sold on the Dark Web (Predictive Threat Intel)?
If a server has a CVSS 10 vulnerability but is buried deep in a segmented VLAN with no internet access and no sensitive data, the AI lowers its priority. Conversely, it will instantly escalate a CVSS 7 vulnerability on a public-facing web server if Threat Intel indicates it is currently being exploited in the wild.
3. Automated Sandbox Testing and Deployment
Once prioritized, the “healing” begins. AI eliminates the fear of deployment through automated validation.
- Digital Twin Testing: Before pushing a patch to production, the AI deploys it to a “Digital Twin”—a virtual, sandbox replica of the specific server or endpoint.
- Behavioral Baseline Comparison: The AI runs synthetic traffic through the patched sandbox. It compares the application’s performance (CPU usage, memory leaks, crash logs) against its pre-patch baseline.
- Autonomous Rollout (or Rollback): If the patch passes the behavioral test, the AI orchestrates the deployment to production in staggered rings (e.g., 5% of machines, then 20%, then 100%). If an anomaly is detected at any stage, the AI autonomously halts the deployment and rolls back the affected machines to their previous healthy state in milliseconds.
4. Virtual Patching and Dynamic Isolation
Sometimes, a system cannot be patched. Perhaps it’s a legacy medical device or an industrial control system (SCADA) running an unsupported OS.
In a self-healing network, if the AI determines a system cannot be patched natively, it applies a Virtual Patch. It dynamically reconfigures the surrounding network infrastructure—updating Web Application Firewalls (WAF) or Intrusion Prevention Systems (IPS)—to look for and block the specific network traffic associated with that exploit.
Alternatively, it can use software-defined networking (SDN) to instantly microsegment the vulnerable machine, isolating it from the rest of the network until a human engineer can review the situation.
Conclusion
Self-healing networks represent a fundamental shift in IT operations. By using AI to assess risk, test updates, and dynamically reconfigure defenses, organizations can dramatically reduce their attack surface—across on-premises infrastructure, cloud environments, and containerized workloads—without sacrificing uptime. We are moving toward a future where the network acts like a biological immune system: automatically detecting vulnerabilities and applying the “antibodies” (patches) before the infection can spread.
