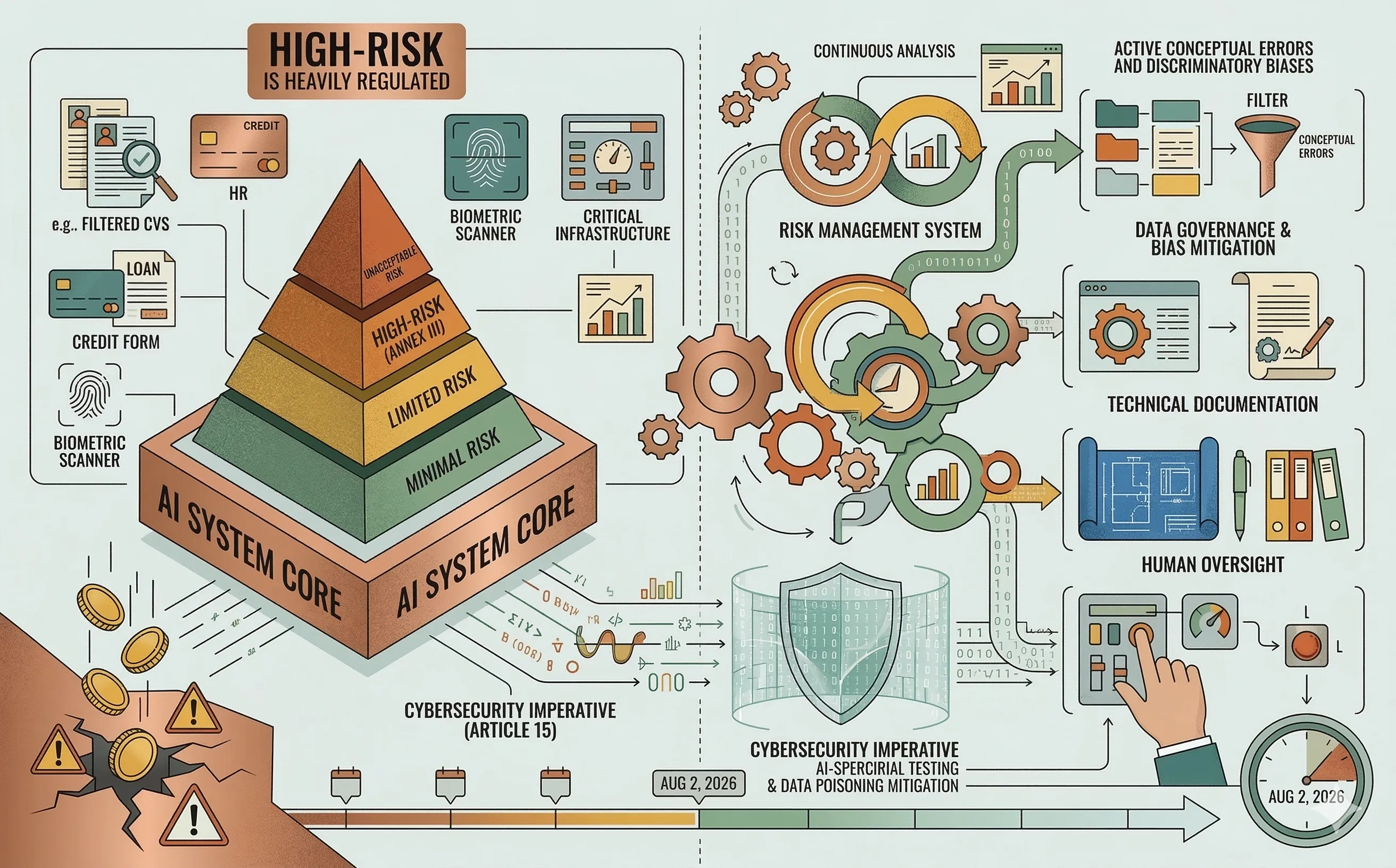
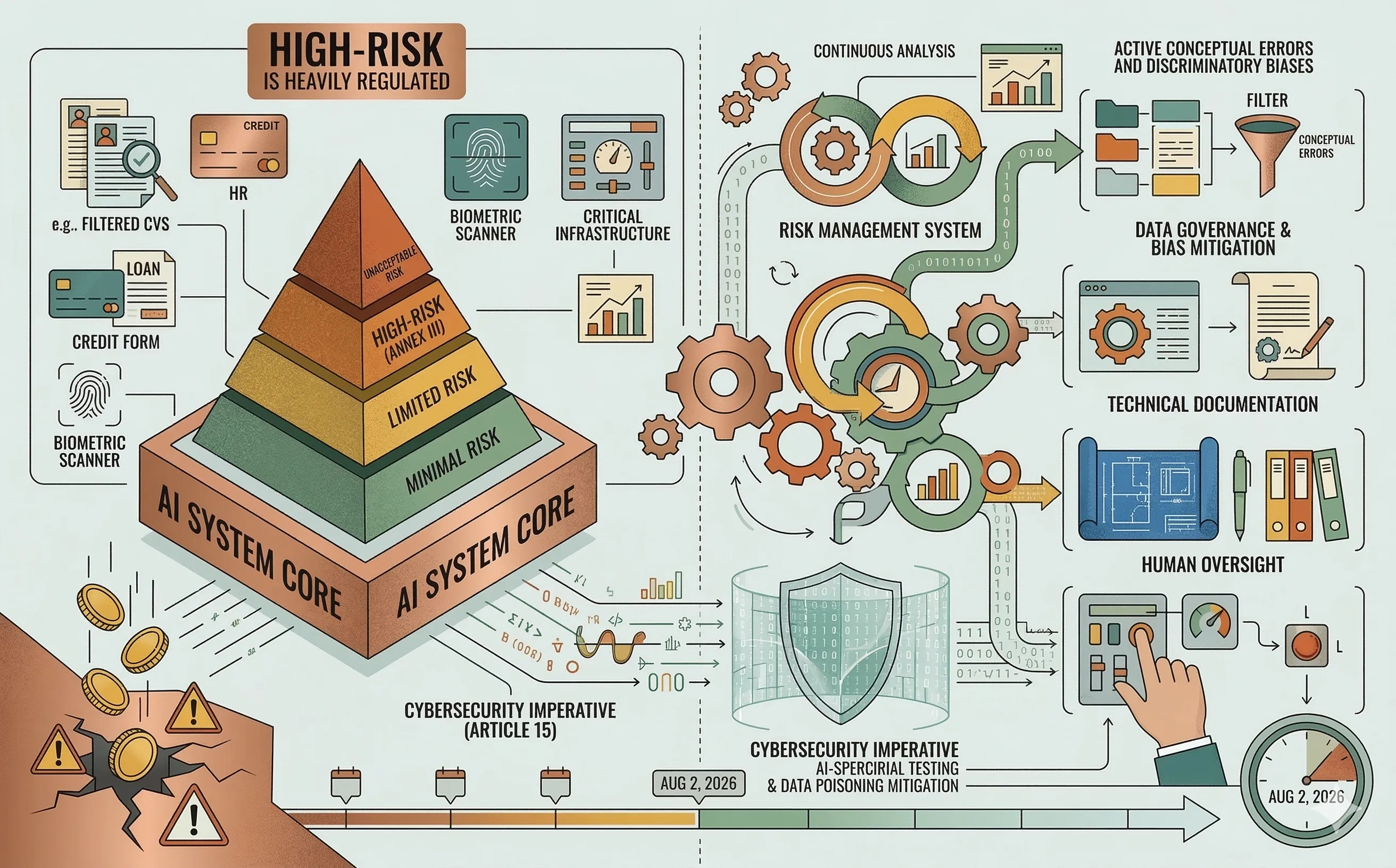
The EU AI Act: Compliance Requirements for High-Risk Systems
Understand the EU AI Act's impact on enterprise IT. Learn the classification of high-risk AI systems and the mandatory compliance requirements for organizations ahead of the 2026 deadline.
Series
Strategic perspectives on AI regulation (EU AI Act), data sovereignty, and the ethical implications of automated decision-making in cybersecurity.
Understand the EU AI Act's impact on enterprise IT. Learn the classification of high-risk AI systems and the mandatory compliance requirements for organizations ahead of the 2026 deadline.
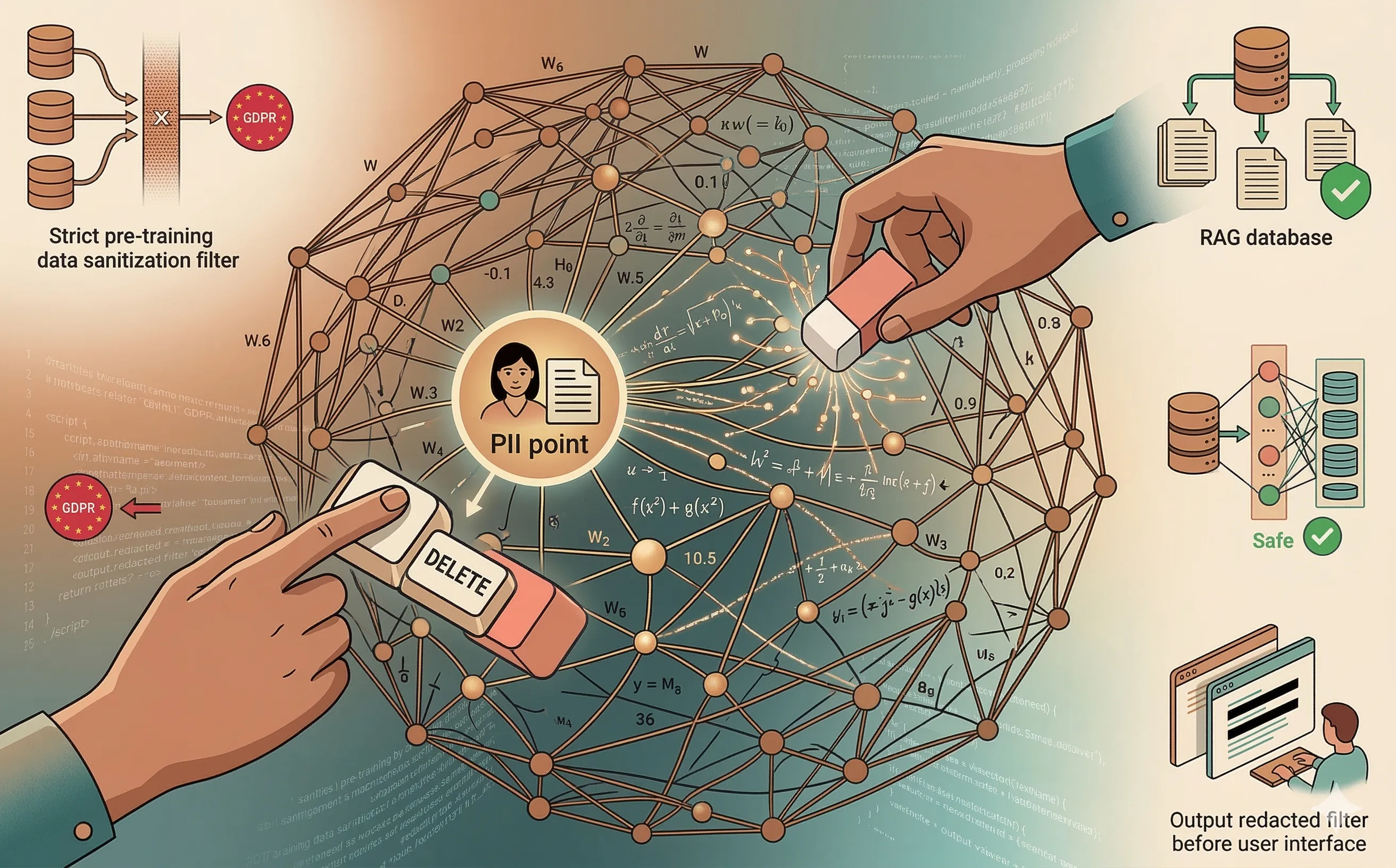
Explore the technical and legal conflict between the GDPR's Right to Erasure and the probabilistic architecture of Large Language Models, and how enterprise IT can adapt.
Explore the legal paradox of AI-generated code. Understand the U.S. Copyright Office rulings, the risk of open-source infringement, and how to protect enterprise IP.

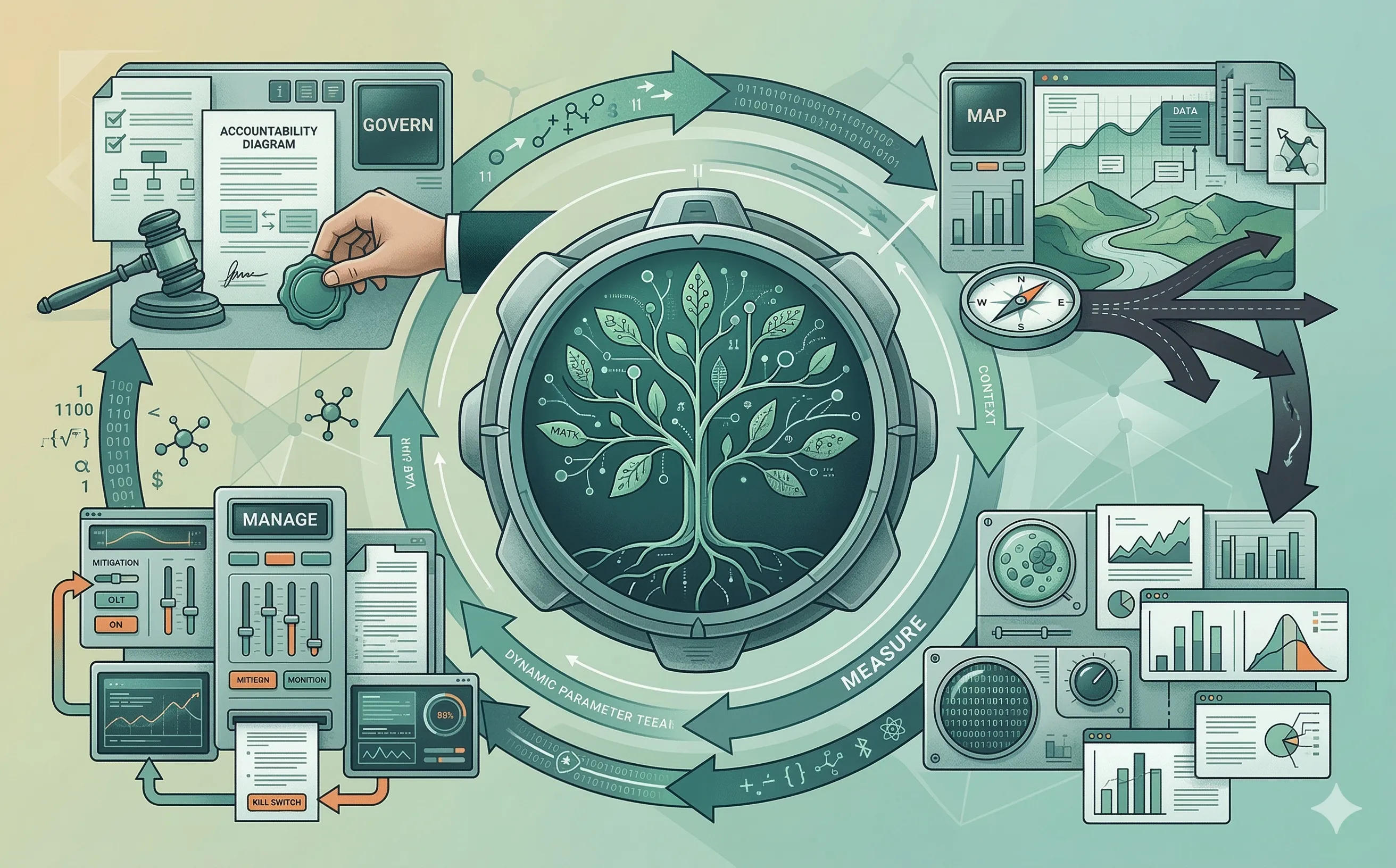
Discover how the NIST AI RMF helps organizations map, measure, and manage AI risks. Learn how to implement this critical framework for trustworthy AI.
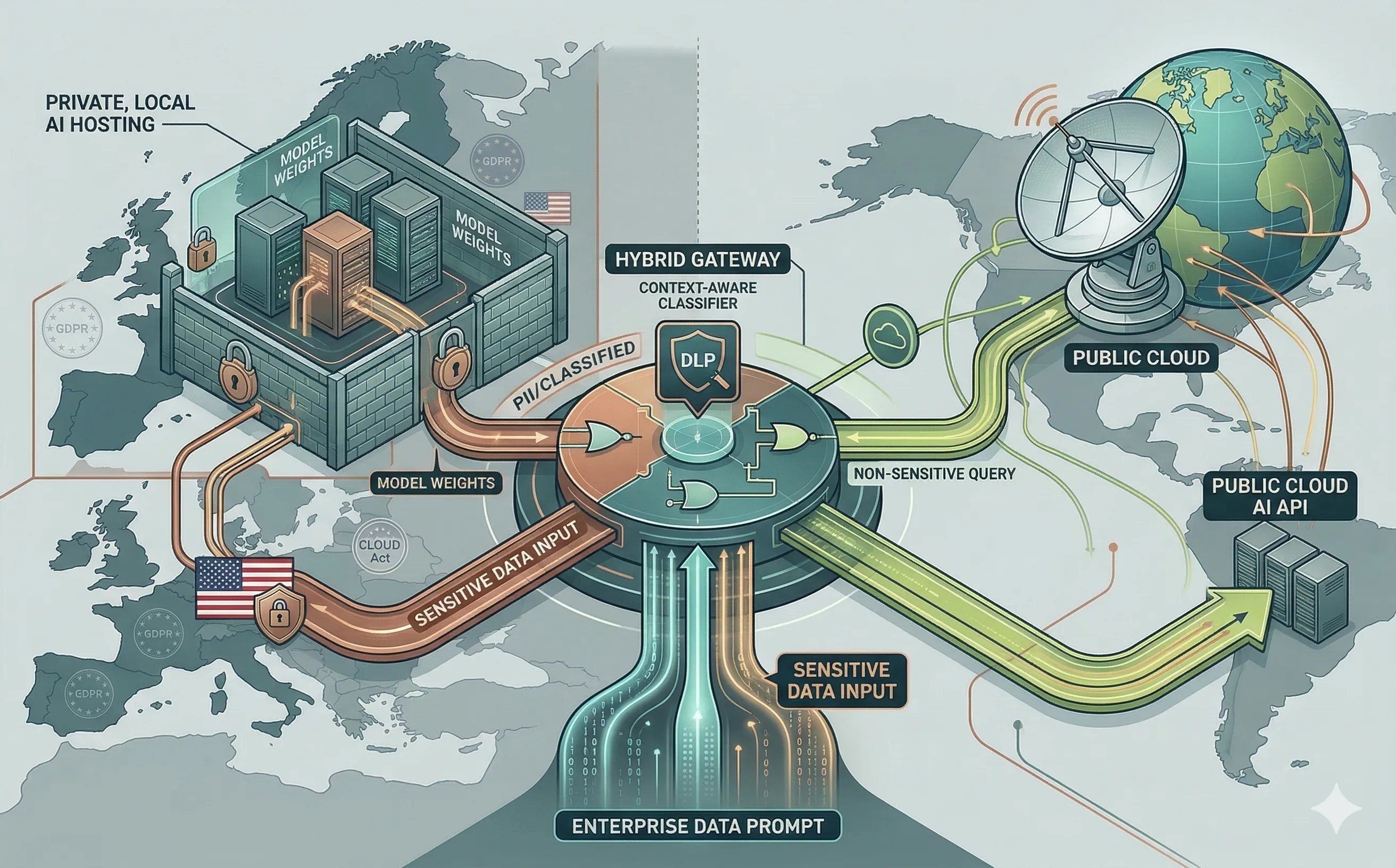
Navigate the data sovereignty dilemma in enterprise AI. Compare the risks of public cloud LLM APIs against the security of hosting private, open-weight models on-premise.
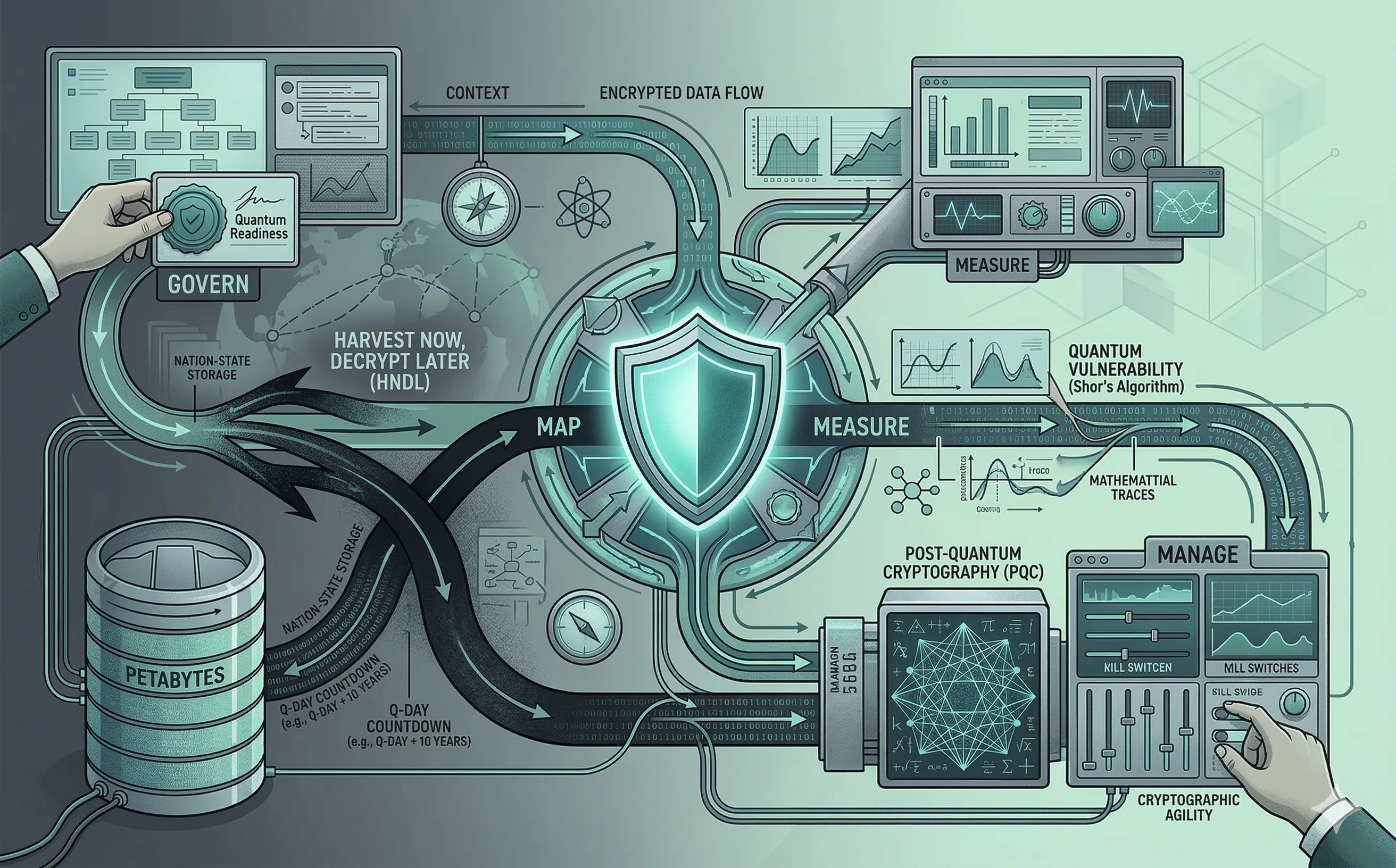
Understand the looming threat of quantum computing on modern cryptography. Explore the 'Harvest Now, Decrypt Later' risk and the strategic transition to Post-Quantum Cryptography (PQC).
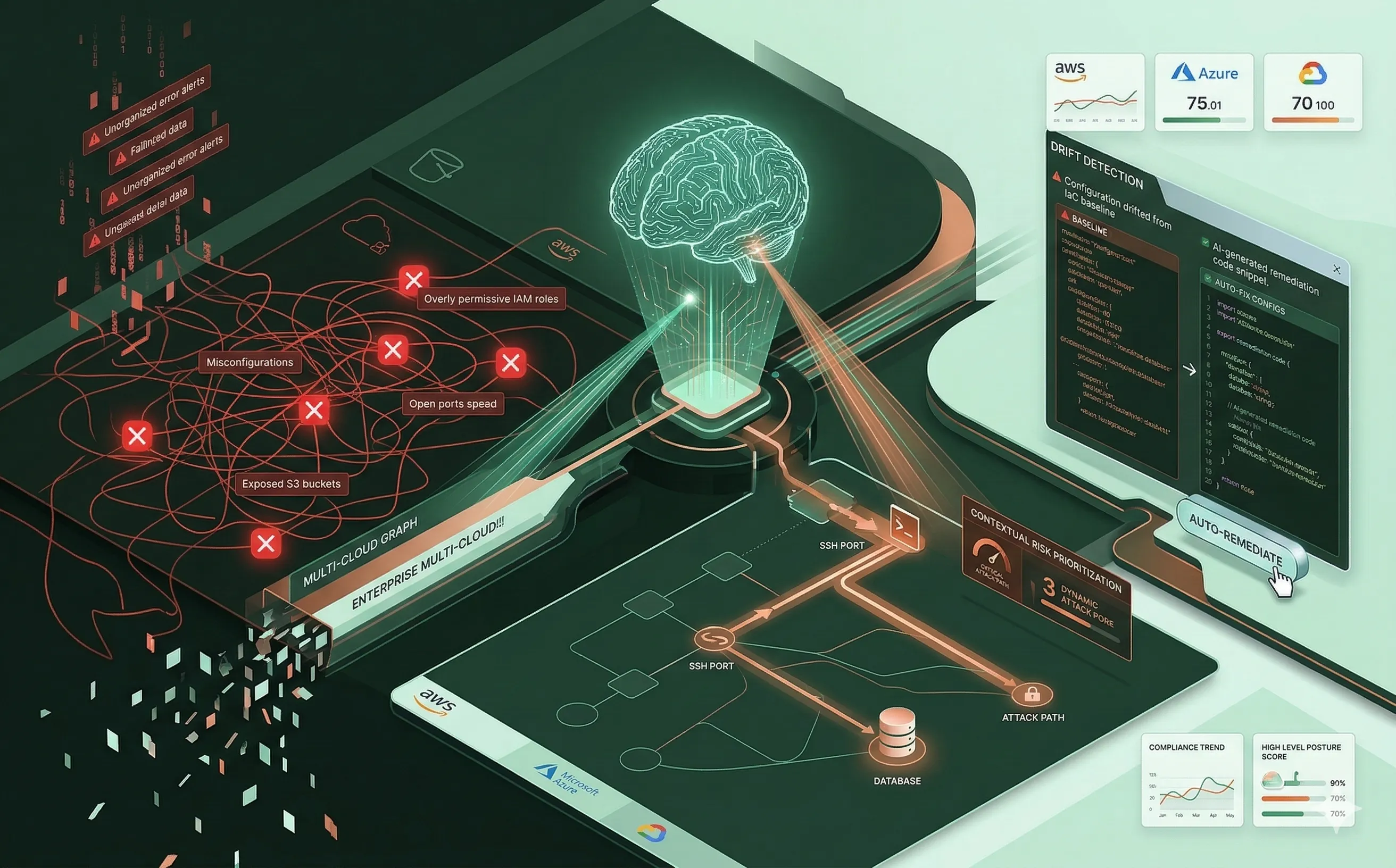
Discover how Artificial Intelligence is transforming CSPM, moving cloud security from noisy, static alerts to contextual, auto-remediated posture management.
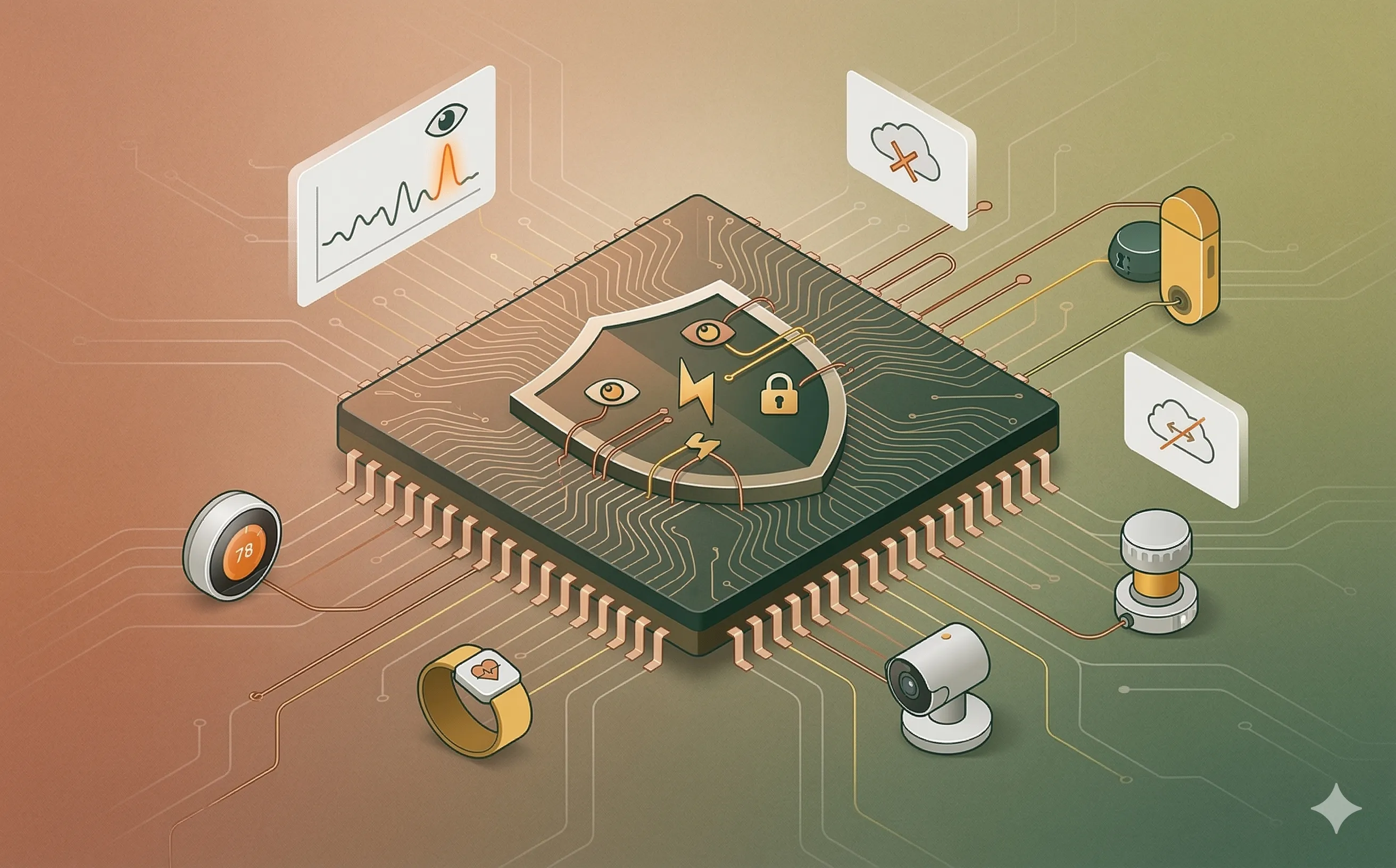
Discover how TinyML and lightweight machine learning models are securing the Internet of Things, bringing real-time anomaly detection to resource-constrained edge devices.
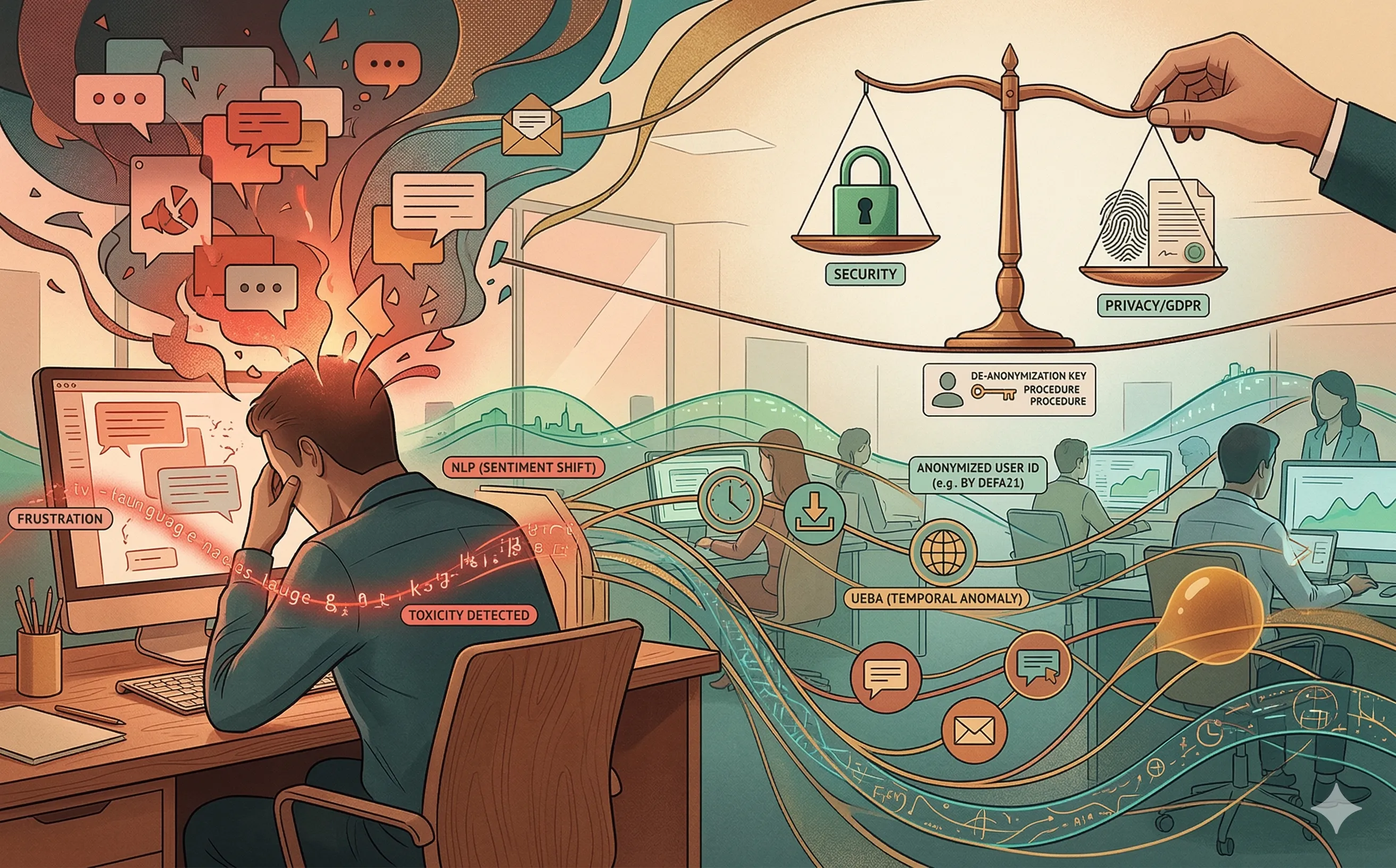
Explore how AI-driven UEBA and sentiment analysis detect malicious insider threats. Navigate the ethical and legal boundaries of monitoring employee behavior.
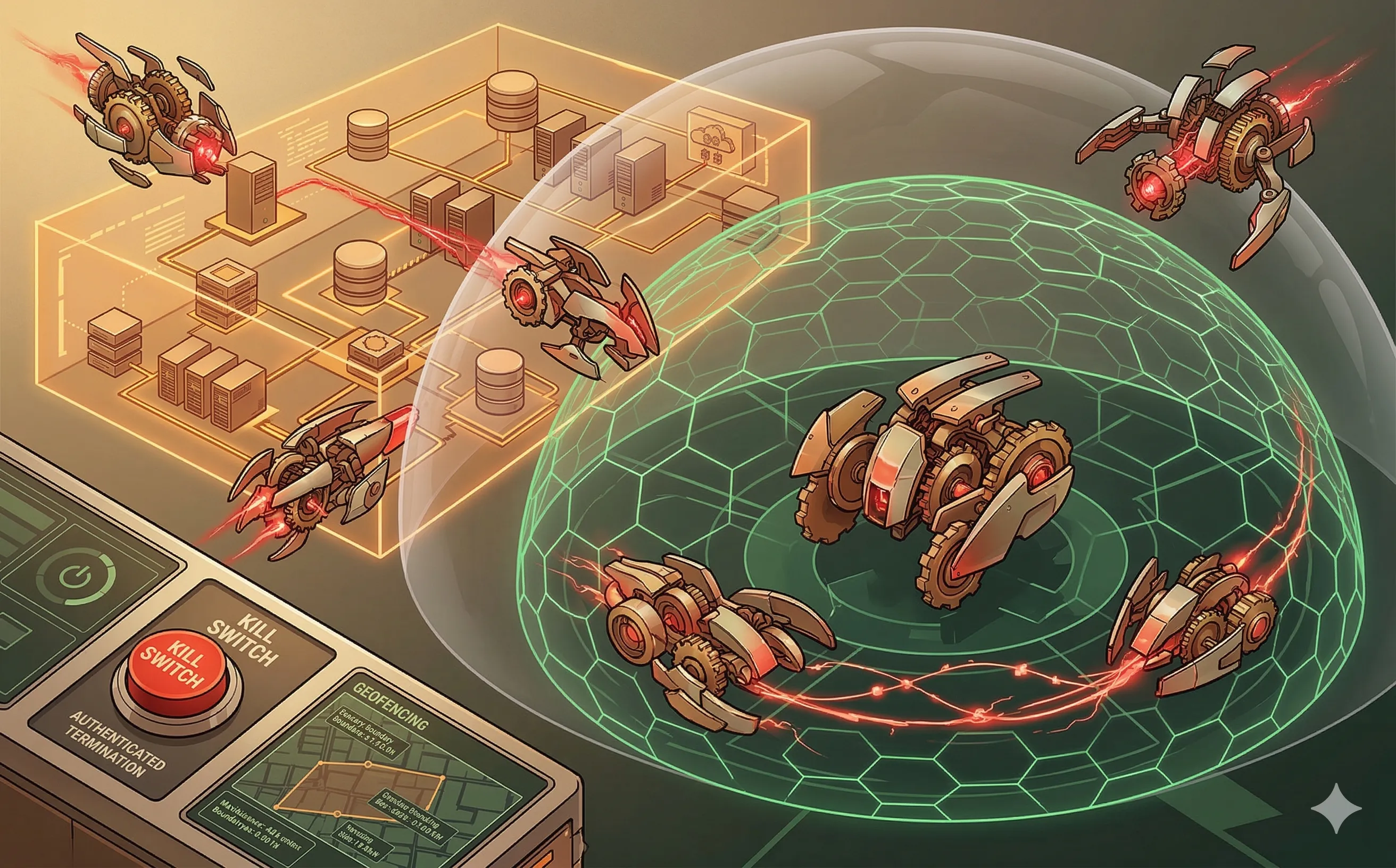
Explore how AI is revolutionizing ethical hacking and Red Teaming. Discover the strategic benefits and governance requirements of automated adversarial emulation.
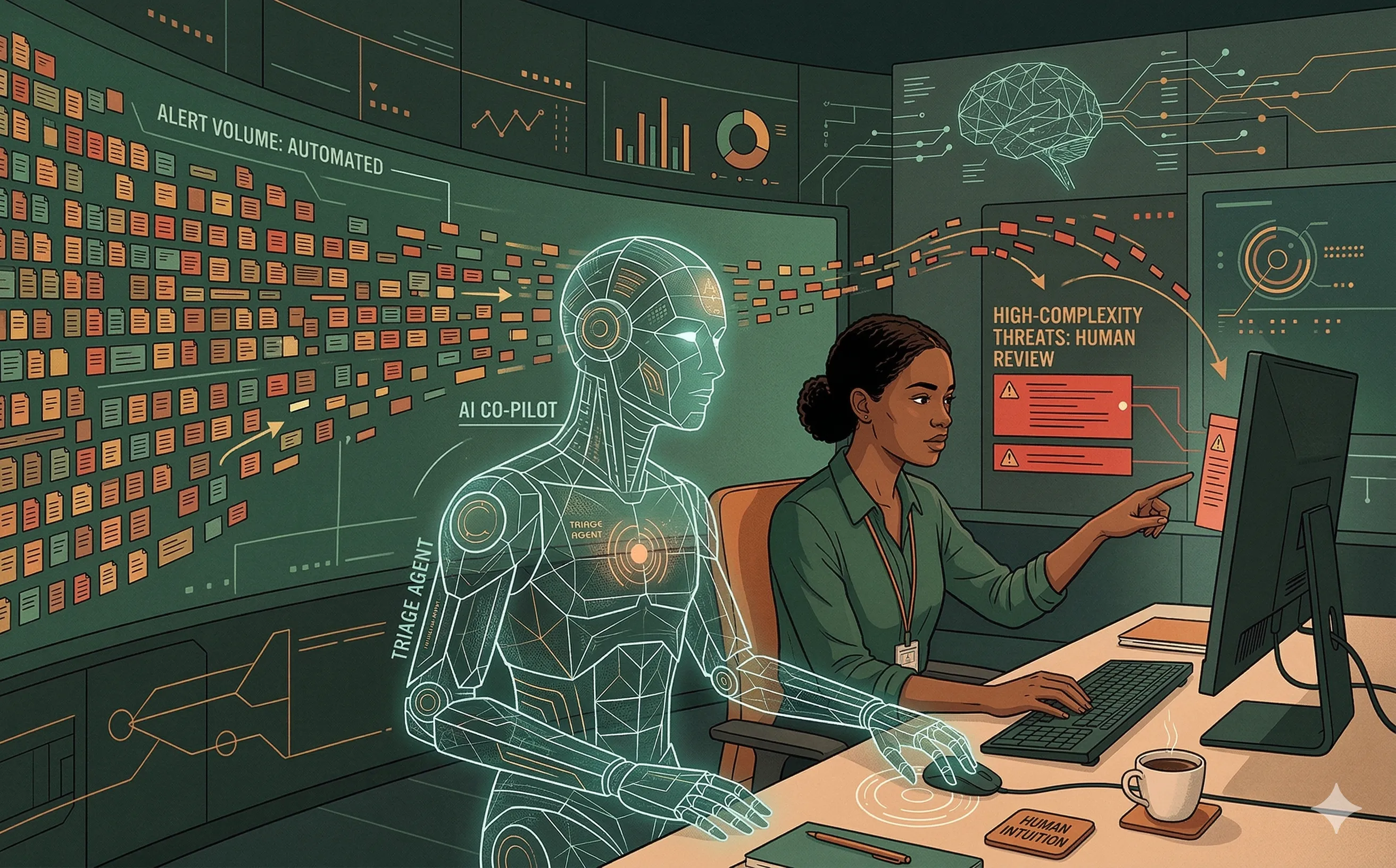
Analyze the impact of AI on the cybersecurity workforce. Discover how the automation of the SOC is redefining entry-level roles and the future of IT talent pipelines.
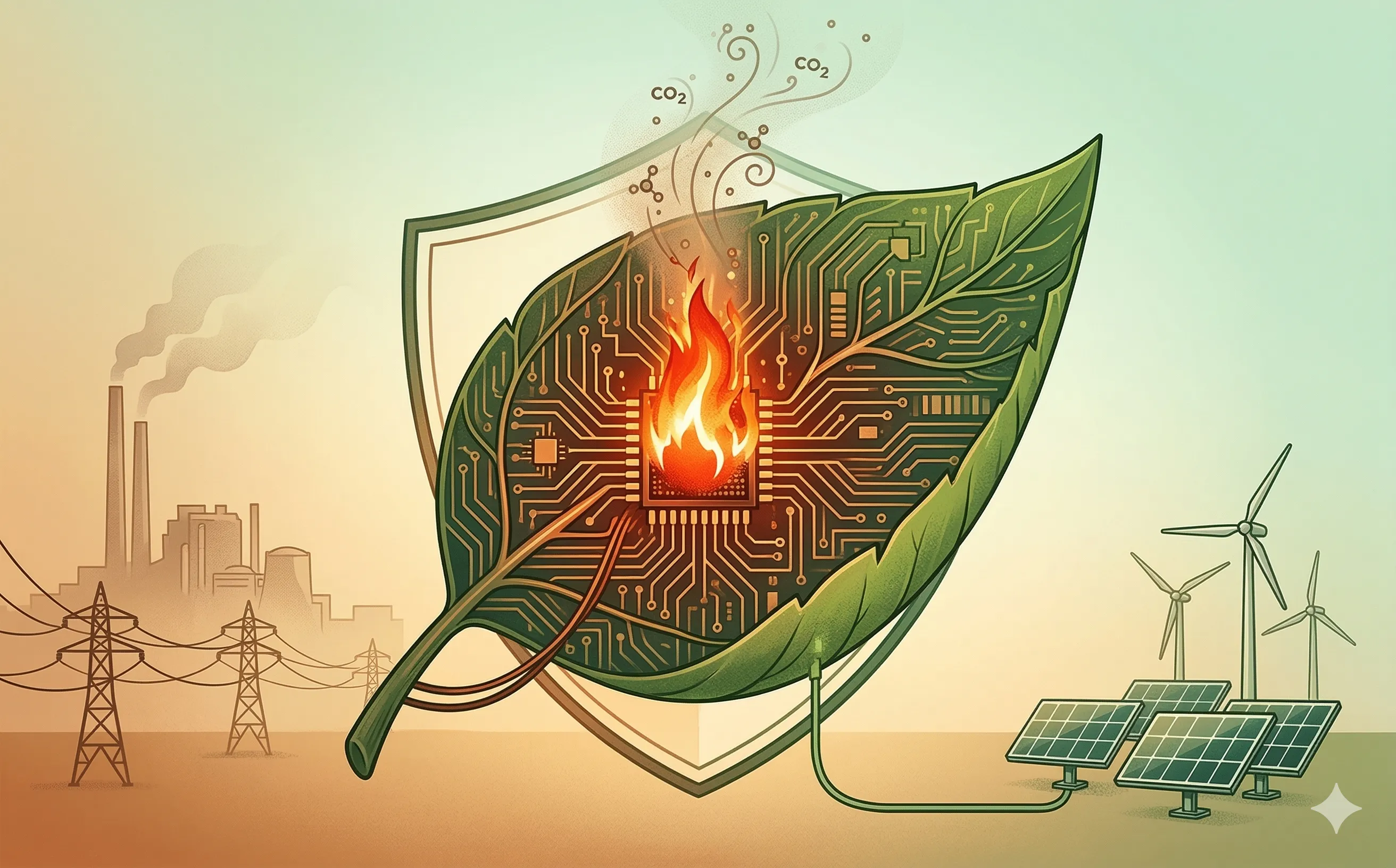
Analyze the intersection of Green IT and cybersecurity. Understand the massive carbon footprint of AI-driven security tools and how to build a sustainable DevSecOps architecture.
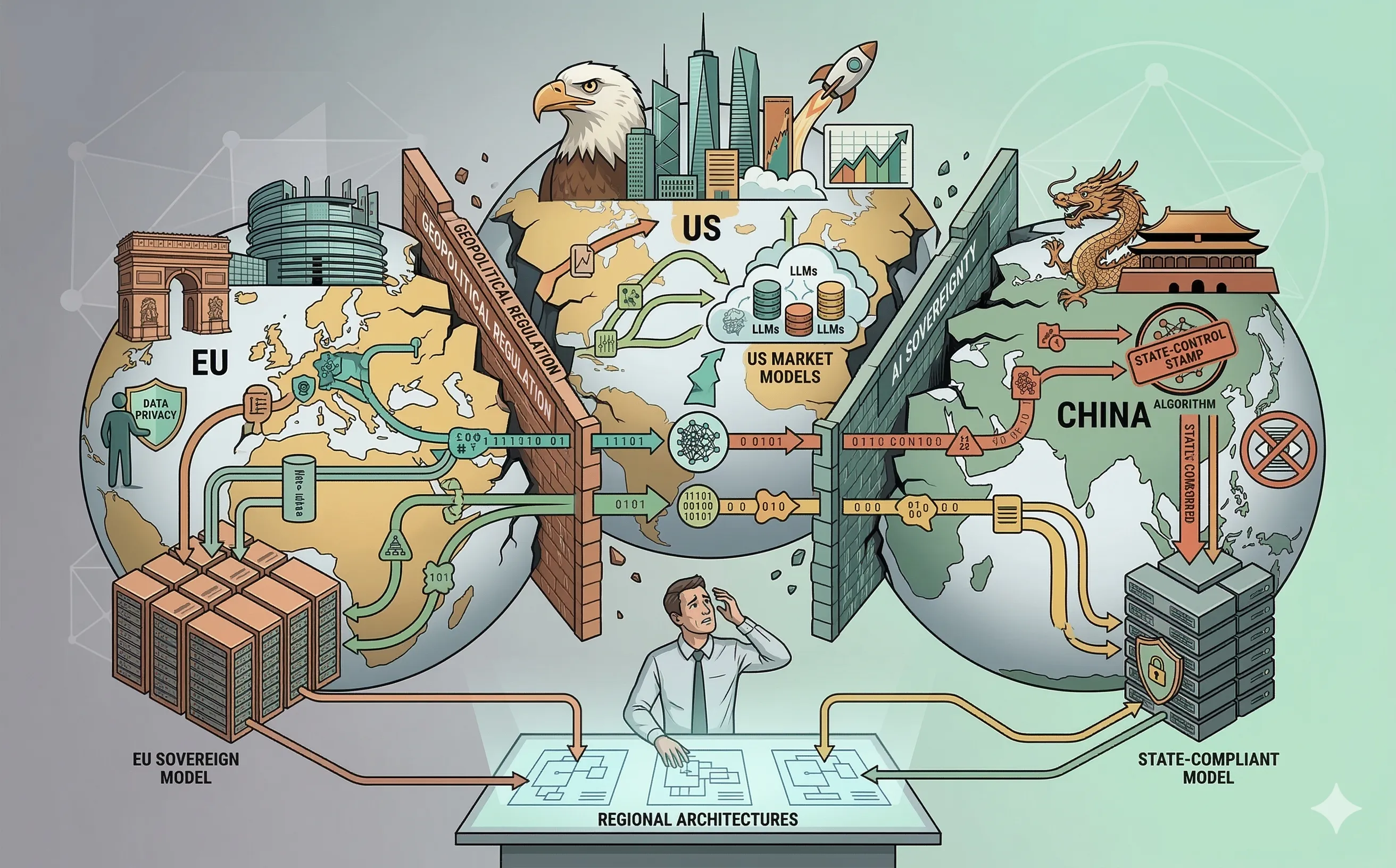
Explore the rise of the AI Splinternet. Understand how divergent geopolitical regulations in the EU, US, and China are forcing enterprise IT to build fragmented, region-specific architectures.