Governance of AI Defense: Ensuring Your Defensive AI Isn't Biased
Explore the risks of algorithmic bias in cybersecurity. Learn how Explainable AI (XAI) and governance prevent defensive models from making discriminatory decisions.

Explore the risks of algorithmic bias in cybersecurity. Learn how Explainable AI (XAI) and governance prevent defensive models from making discriminatory decisions.

Learn how XDR breaks down security silos by using AI to correlate telemetry from endpoints, networks, identities, and the cloud for proactive threat hunting.

Explore how Next-Generation Firewalls use inline deep learning to stop zero-day attacks, detect DGA traffic, and secure unmanaged IoT devices in real-time.

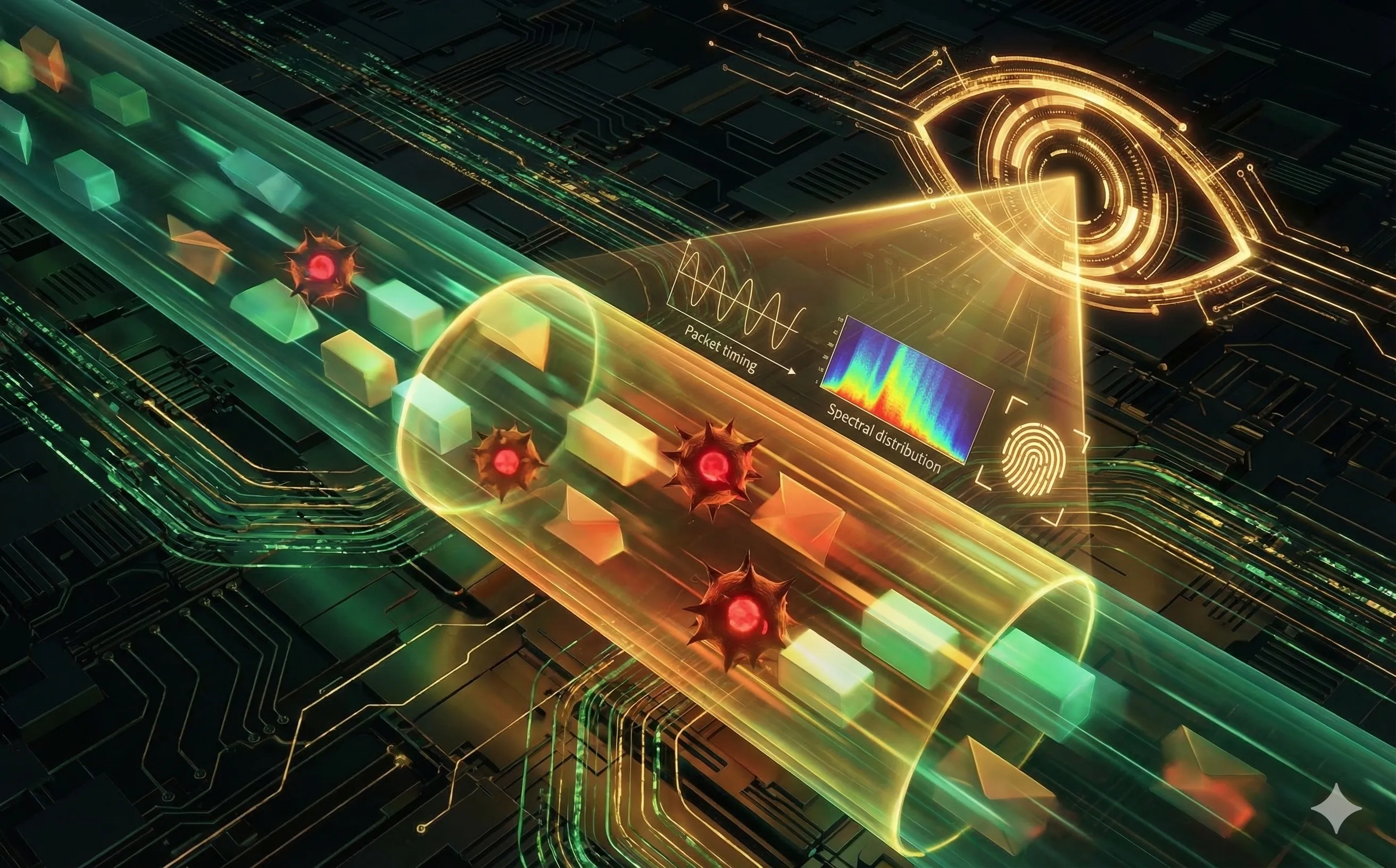
Learn how AI-powered Network Traffic Analysis (NTA) detects malware and data exfiltration hidden inside encrypted HTTPS and TLS traffic without decrypting it.
Learn how AI-powered EDR agents use local machine learning models to detect fileless malware, ransomware, and zero-day threats in real-time.

Explore how modern Secure Email Gateways use Natural Language Processing (NLP) and Semantic AI to detect advanced phishing and Business Email Compromise.

Learn how AI-driven deception technology creates dynamic honeypots and fake network assets to trap attackers, waste their time, and gather threat intel.

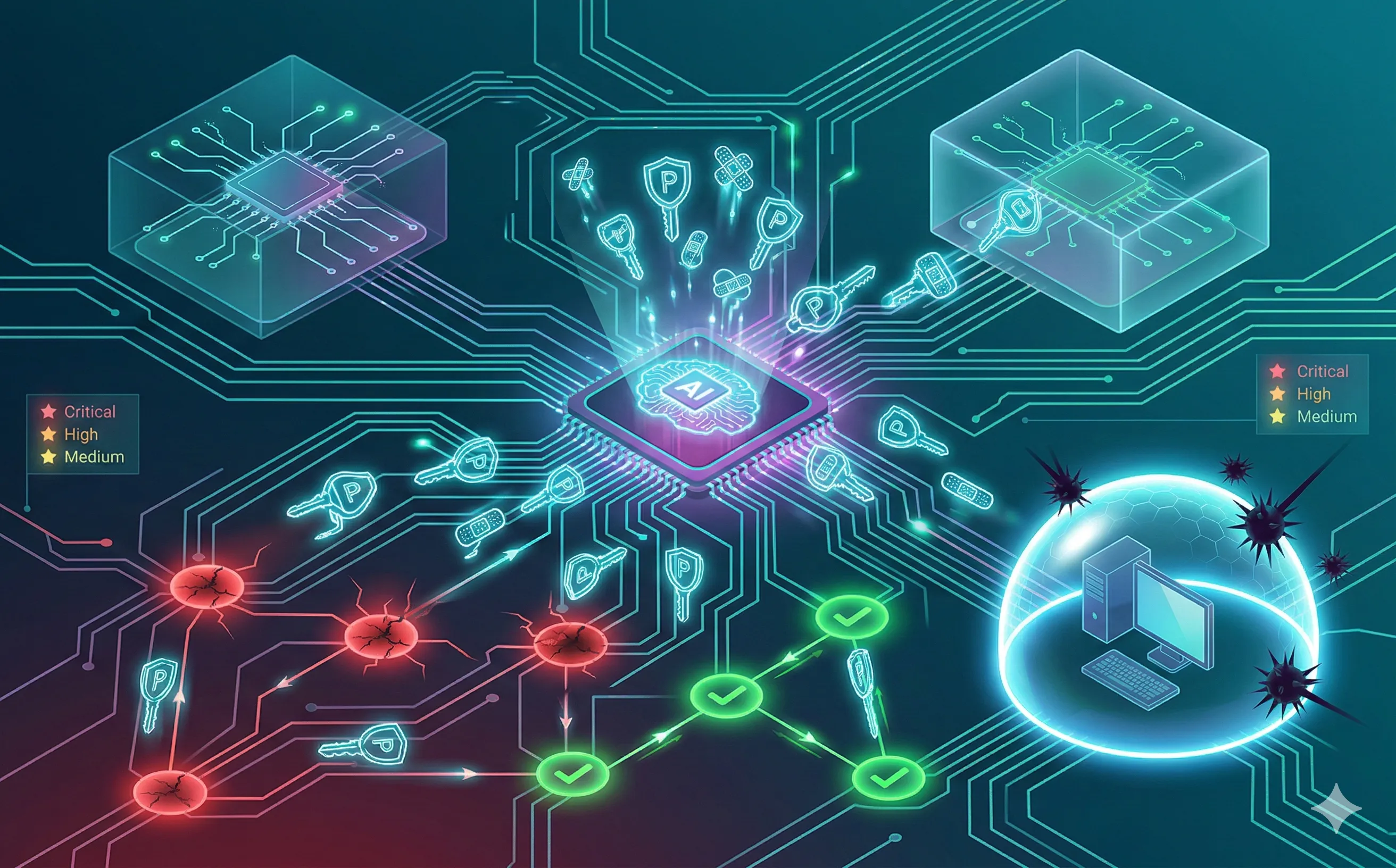
Discover how AI-driven self-healing networks automate patch management, prioritize vulnerabilities, and dynamically isolate unpatched systems.
Learn how cybersecurity teams use AI-powered liveness detection and multispectral analysis to defeat deepfakes and secure biometric authentication.

Explore how Artificial Intelligence powers modern Zero Trust Architectures through continuous authentication, dynamic risk scoring, and microsegmentation.

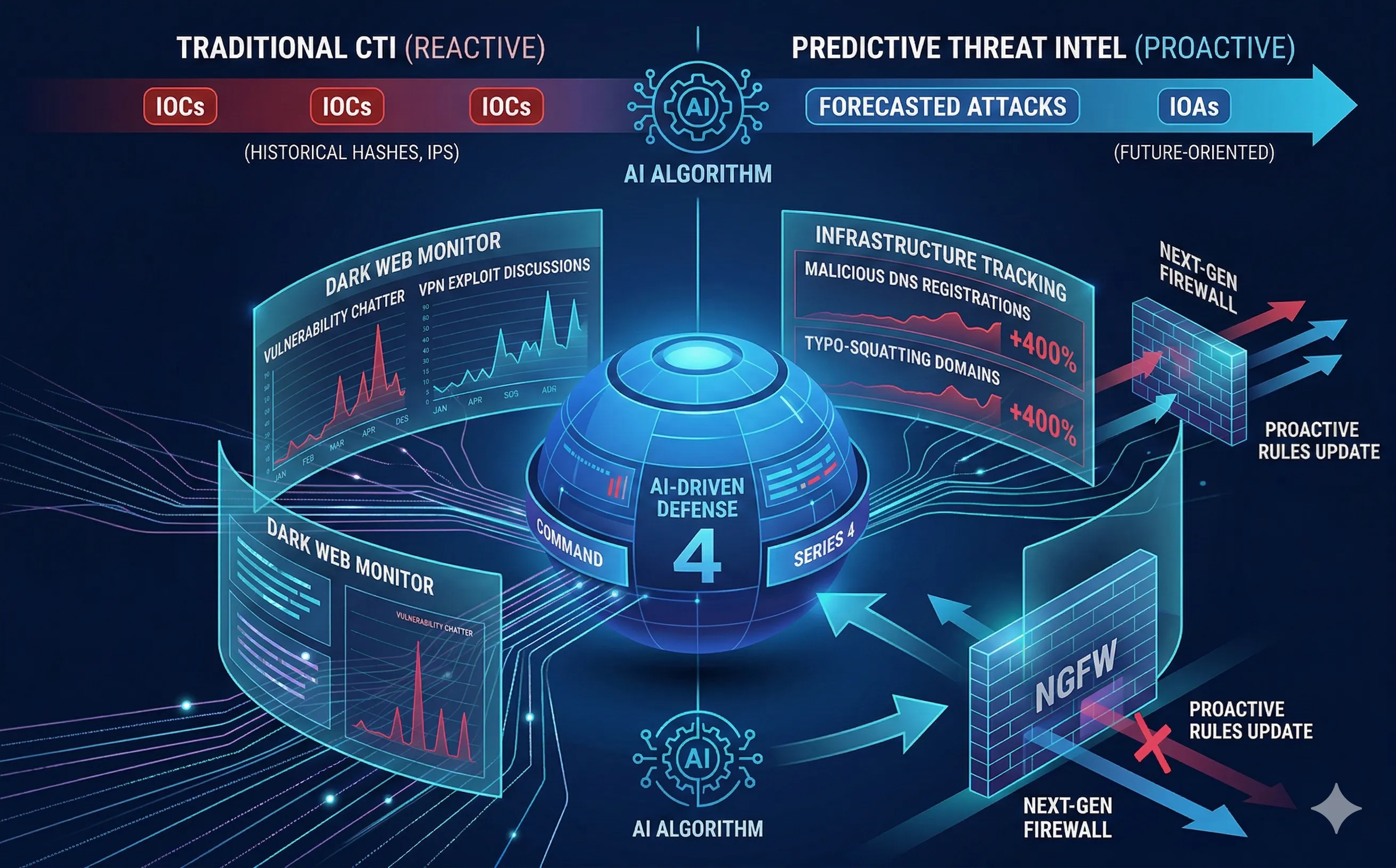
Discover how AI transforms Threat Intelligence from reactive blacklists into predictive models that forecast cyberattacks before they happen.
Learn how SOAR platforms use AI and automated playbooks to orchestrate incident response, isolate threats, and drastically reduce MTTR in the SOC.

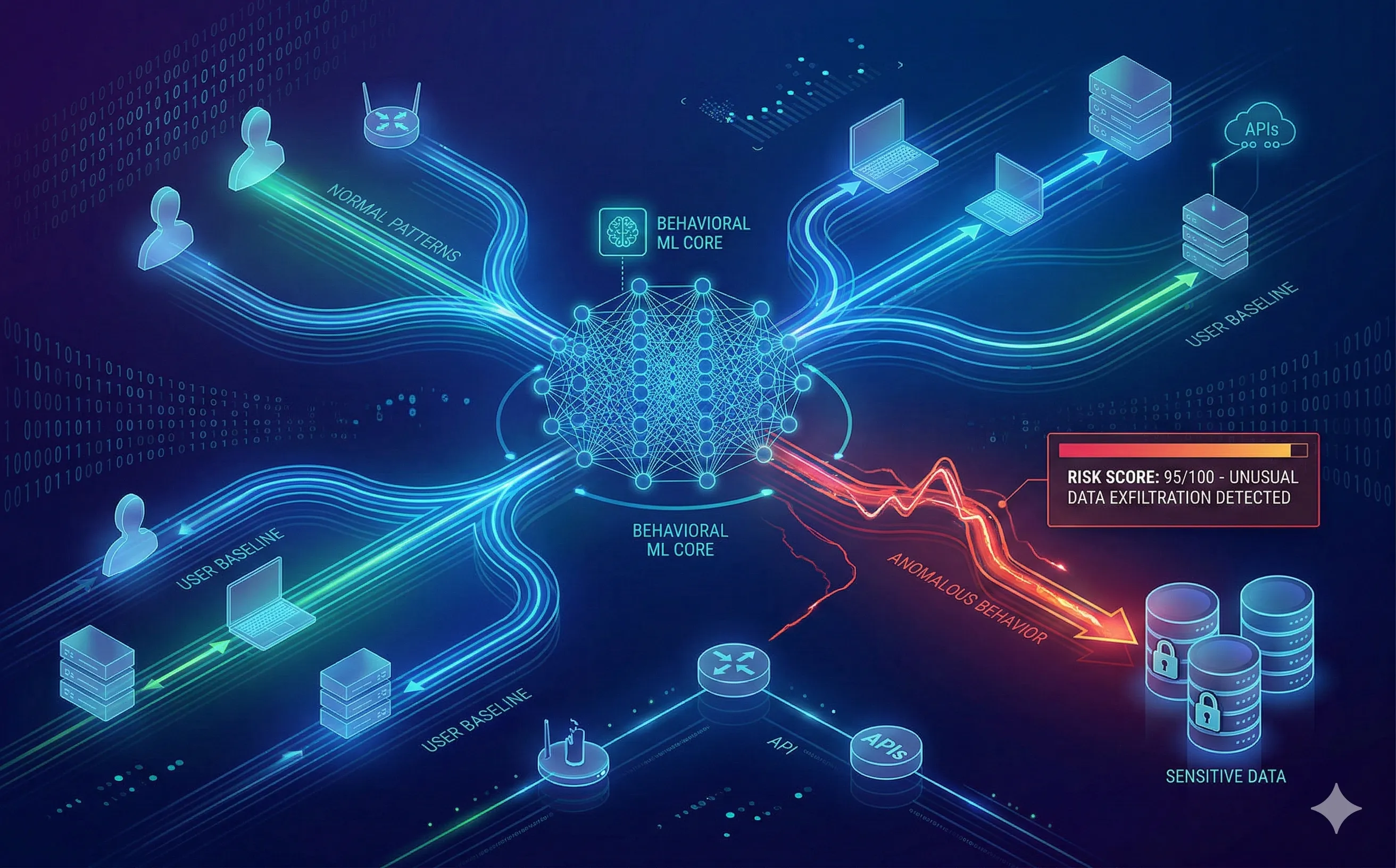
Discover how UEBA uses Machine Learning to baseline user behavior, detect anomalies, and stop insider threats or compromised credentials in real-time.