Mobile App Security: AI Threats to iOS and Android
Explore how AI is changing mobile app security. Learn about deepfake biometric bypasses, AI-automated repackaging, and protecting on-device ML models.

Explore how AI is changing mobile app security. Learn about deepfake biometric bypasses, AI-automated repackaging, and protecting on-device ML models.

Learn how AI and machine learning enhance Kubernetes security by detecting anomalous container behavior, zero-day exploits, and lateral movement at runtime.

Explore how AI is fueling a new generation of sophisticated bots and how DevSecOps teams use behavioral biometrics and ML to block them.

Discover how AI and Machine Learning transform API security by detecting Shadow APIs, BOLA attacks, and anomalous usage patterns in modern microservices.

Explore how Machine Learning is transforming SAST and DAST, reducing false positives, and detecting complex vulnerabilities in modern applications.
Learn how XDR breaks down security silos by using AI to correlate telemetry from endpoints, networks, identities, and the cloud for proactive threat hunting.

Learn how AI-powered Network Traffic Analysis (NTA) detects malware and data exfiltration hidden inside encrypted HTTPS and TLS traffic without decrypting it.
Learn how AI-powered EDR agents use local machine learning models to detect fileless malware, ransomware, and zero-day threats in real-time.

Explore how modern Secure Email Gateways use Natural Language Processing (NLP) and Semantic AI to detect advanced phishing and Business Email Compromise.

Explore how Artificial Intelligence powers modern Zero Trust Architectures through continuous authentication, dynamic risk scoring, and microsegmentation.

Discover how AI transforms Threat Intelligence from reactive blacklists into predictive models that forecast cyberattacks before they happen.
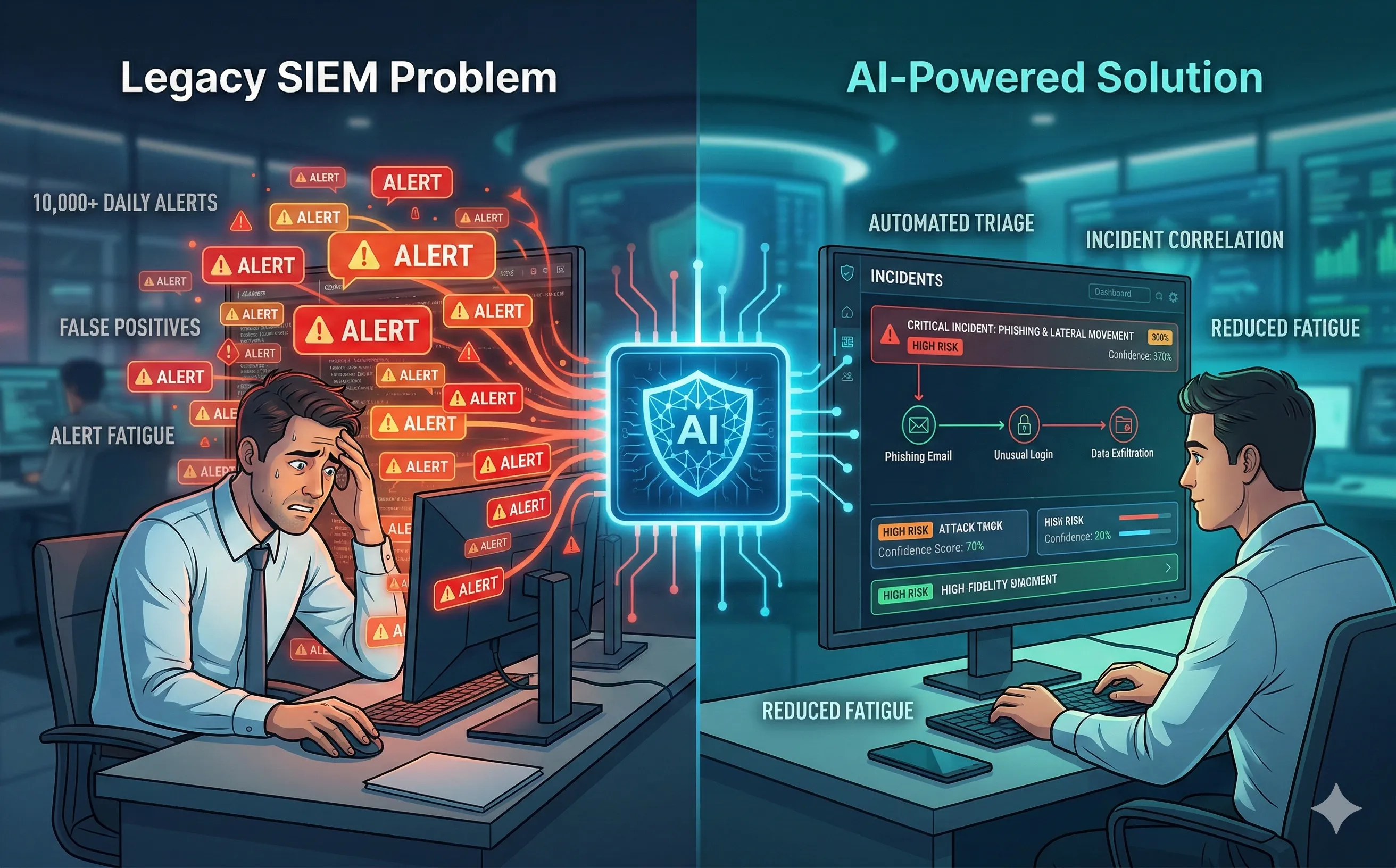
Discover how AI-powered SIEMs reduce alert fatigue for SOC analysts. Learn how machine learning automates threat triage and correlation for faster response.
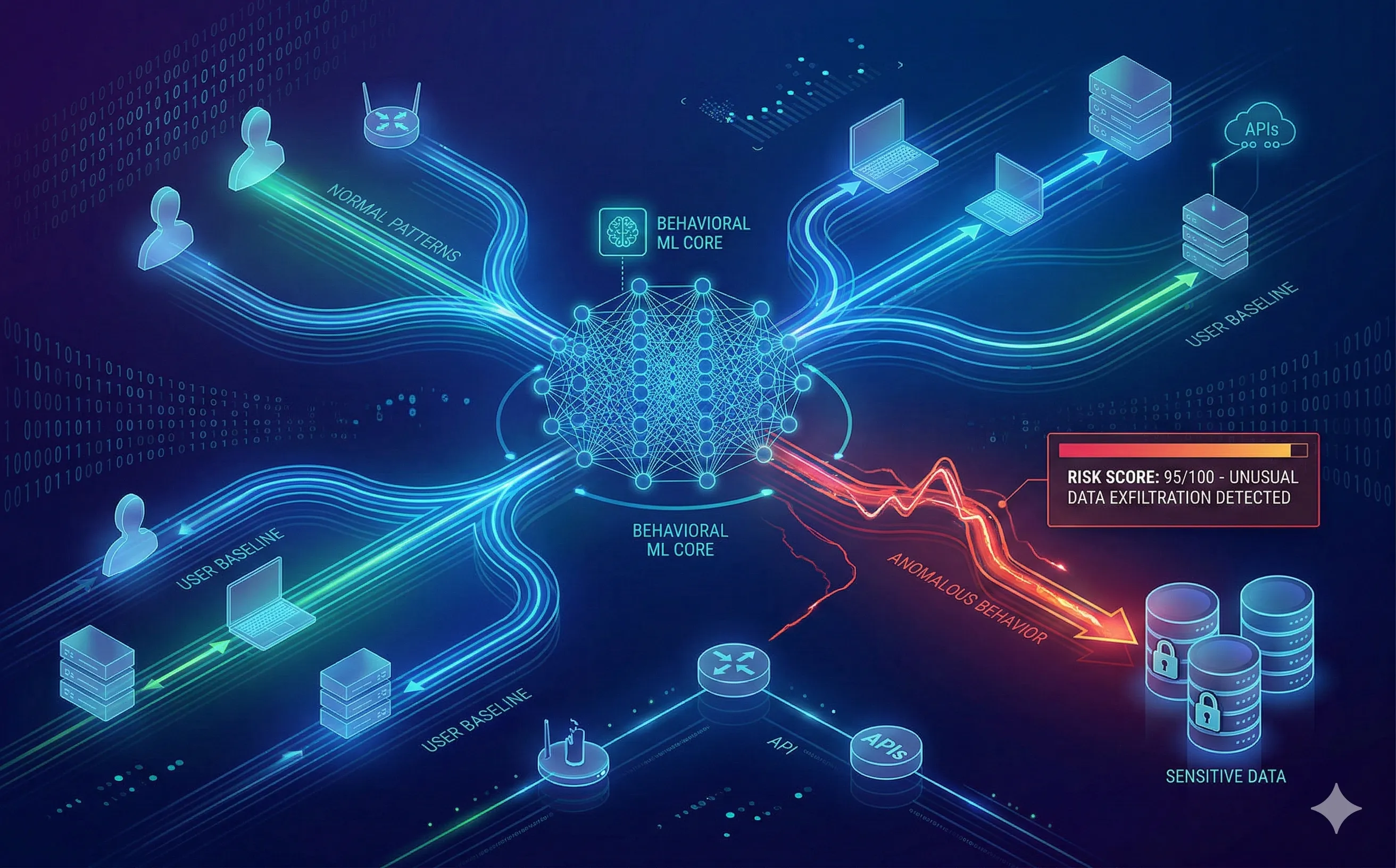
Discover how UEBA uses Machine Learning to baseline user behavior, detect anomalies, and stop insider threats or compromised credentials in real-time.
Explore how adversarial examples and invisible digital noise trick AI vision models. Understand inference-time evasion attacks and physical world implications.