The Skills Gap: Will AI Replace the Junior Cybersecurity Analyst?
Analyze the impact of AI on the cybersecurity workforce. Discover how the automation of the SOC is redefining entry-level roles and the future of IT talent pipelines.
Introduction: The Silver Bullet and the Talent Crisis
For over a decade, the cybersecurity industry has faced a paralyzing structural problem: the global skills gap. With millions of unfilled positions worldwide, Chief Information Security Officers (CISOs) and IT managers have struggled to recruit, train, and retain enough talent to defend against an increasingly automated adversary.
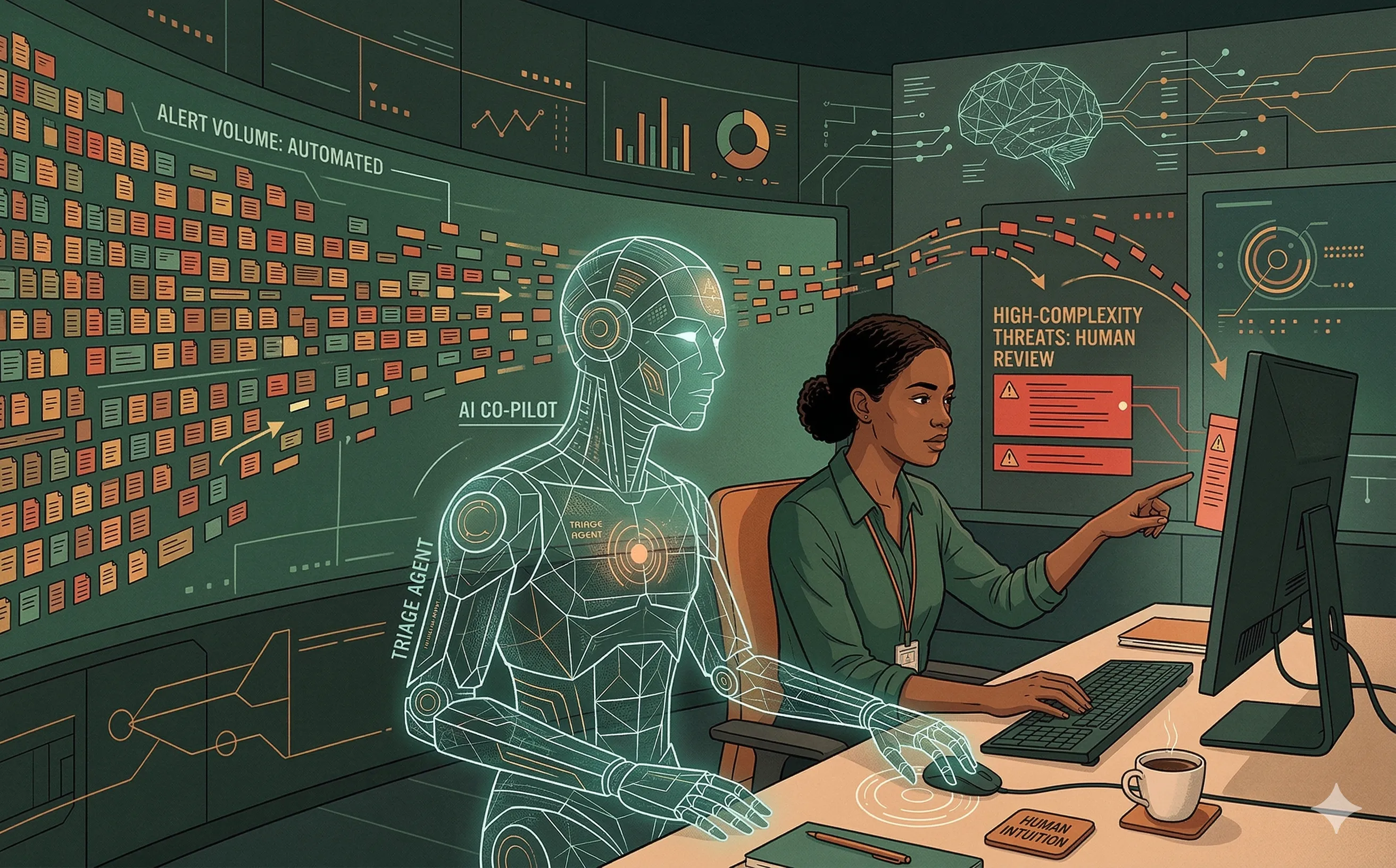
Enter Artificial Intelligence. Vendors are aggressively marketing AI-driven Security Operations Center (SOC) platforms as the ultimate solution to the talent shortage, promising autonomous agents that can instantly triage alerts, hunt threats, and remediate vulnerabilities. This has sparked a controversial and existential question within the industry: Will AI completely replace the Junior Cybersecurity Analyst? For IT leaders and students entering the field, understanding the strategic reality behind the hype is essential for future-proofing your career and your organization.
1. The Death of the “Swivel-Chair” Analyst
To answer the question, we must first look at what a traditional Tier 1 SOC Analyst actually does. Historically, the entry-level cybersecurity job involved staring at a SIEM (Security Information and Event Management) dashboard, waiting for an alert to turn red. The analyst would then copy an IP address, pivot to a second monitor to paste it into VirusTotal or a threat intelligence feed, and write a brief ticket summarizing the findings. This highly repetitive, manual process is known as “swivel-chair” analysis.
This specific iteration of the junior role is absolutely being automated out of existence.
- Machine-Speed Triage: AI agents do not suffer from alert fatigue. Large Language Models (LLMs) integrated into the SOC can ingest 10,000 alerts, query threat intelligence databases via API, parse the resulting JSON, and generate a natural-language summary of the incident in milliseconds.
- Auto-Remediation: For low-complexity, high-confidence threats (e.g., a known malicious IP attempting an SSH brute force), the AI can be pre-authorized to automatically update firewall rules and isolate the endpoint without ever waking up a human.
2. The Paradox of the “Missing Junior”
If AI successfully automates the bottom tier of the SOC, IT management faces a severe, long-term strategic crisis: How do you create Senior Analysts if there are no Junior Analysts?
You cannot mint a Tier 3 Incident Responder or a master Threat Hunter out of thin air. The intuition required to navigate a complex, multi-stage ransomware negotiation or reverse-engineer a novel piece of malware is forged in the crucible of Tier 1 grunt work. By reading thousands of mundane logs, a junior analyst slowly builds a mental model of what “normal” network traffic looks like.
If we outsource all the foundational learning to a machine, we risk breaking the talent pipeline entirely. In five years, organizations may find themselves with highly efficient AI systems, but absolutely no human experts capable of managing, auditing, or rescuing those systems when they inevitably fail or encounter a true zero-day attack.
3. Redefining the Entry-Level Skillset
The junior cybersecurity role is not disappearing; it is evolving. IT managers must fundamentally rewrite their job descriptions and training programs. The next generation of entry-level analysts will not be manual log-readers; they will be AI Handlers and Automation Engineers.
To survive and thrive, the junior skillset must pivot:
- Prompt Engineering and AI Auditing: Instead of manually querying a database, the new junior analyst will use natural language to command AI to hunt across petabytes of telemetry. Crucially, their primary job will be auditing the AI’s output, utilizing critical thinking to spot “hallucinations” or false positives generated by the model.
- Scripting and API Integration: Understanding how to chain tools together is more valuable than knowing how to use one specific vendor’s dashboard. Proficiency in Python and API structures becomes the baseline requirement to build the “connective tissue” between various AI security agents.
- Business Context: AI understands mathematics and probability, but it does not understand office politics or business context. An AI might flag a massive data download by the CFO as an insider threat. A human analyst is required to understand that the CFO is preparing for an unannounced quarterly earnings call and the behavior is legitimate.
4. The Human-in-the-Loop Strategic Imperative
For IT leadership, the deployment of AI in the SOC should be viewed as an augmentation strategy, not a cost-cutting replacement strategy.
- The Empathy and Ethics Gap: Cybersecurity is ultimately a human-centric discipline. When a major breach occurs, it is not an algorithm that calms down a panicked Board of Directors, negotiates with threat actors, or communicates transparently with impacted customers. Empathy, ethical judgment, and strategic communication are entirely human domains.
- Elevating the Workforce: By allowing AI to handle the mind-numbing volume of commodity alerts, IT managers can elevate their junior staff. Entry-level employees can spend their time engaging in proactive threat hunting, developing custom detection engineering rules, and participating in tabletop exercises—activities that actually improve the organization’s security posture and accelerate the employee’s career growth.
Conclusion
Artificial intelligence will not replace the cybersecurity analyst, but a cybersecurity analyst using AI will absolutely replace one who does not. For the enterprise, the goal is not to eliminate the junior workforce, but to redefine it. By treating AI as an incredibly fast, slightly unreliable co-pilot, IT leaders can solve the volume problem of modern cyber defense while simultaneously cultivating a new generation of highly skilled, strategically focused security professionals.
