The "Splinternet": How Geopolitical AI Regulations Fragment the Web
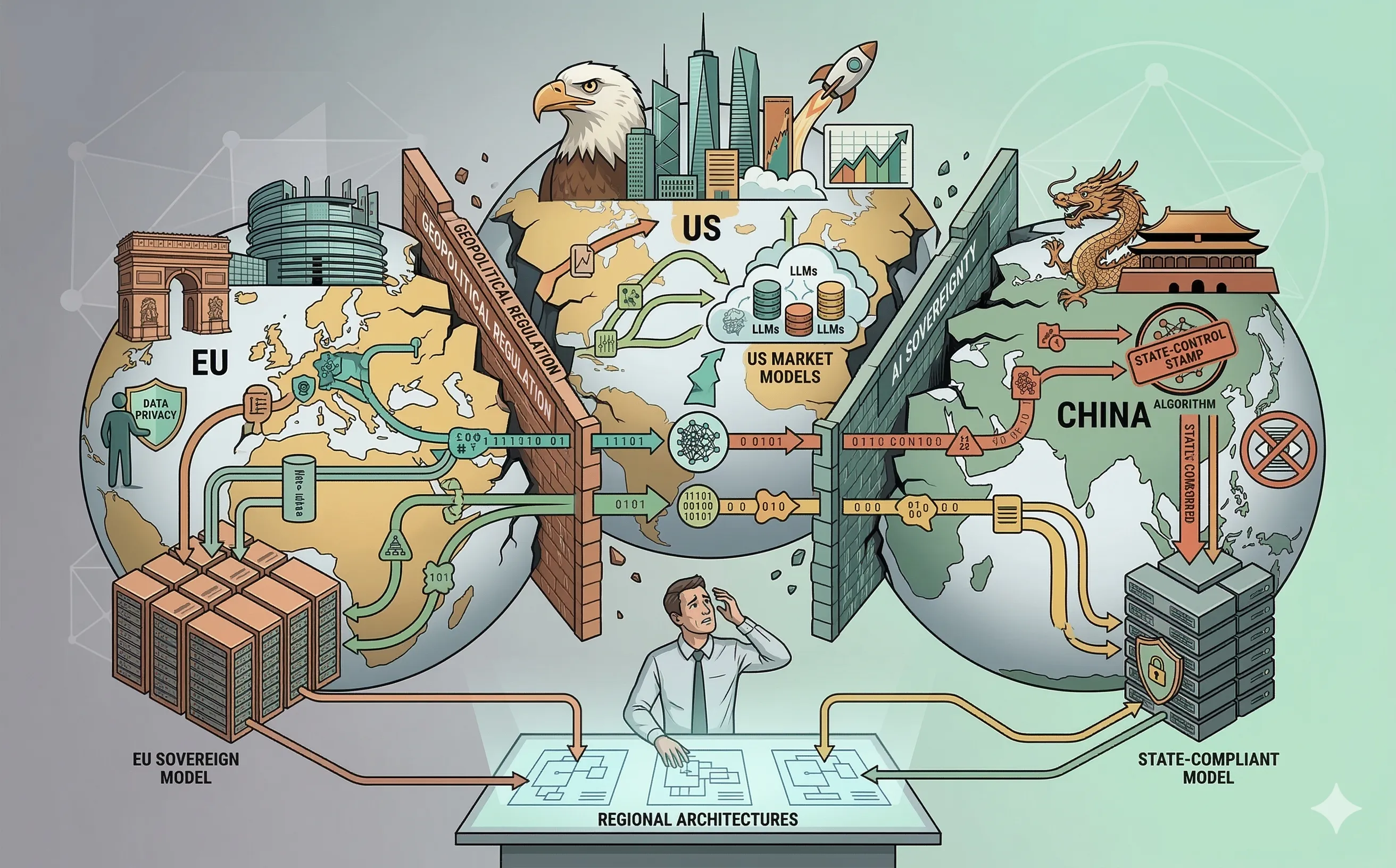
Explore the rise of the AI Splinternet. Understand how divergent geopolitical regulations in the EU, US, and China are forcing enterprise IT to build fragmented, region-specific architectures.
Introduction: The End of the Globalized Web
For the past thirty years, the fundamental promise of the internet was borderless connectivity. An application deployed in Paris could be seamlessly accessed by users in New York or Tokyo, running on the same codebase and governed by roughly the same technical standards. However, the explosive rise of Artificial Intelligence has catalyzed the end of this era.
As nations realize that AI is not just a commercial technology, but a critical engine of national security, economic dominance, and cultural influence, they are erecting massive digital borders. This geopolitical fracturing is creating the “Splinternet”—a fragmented web where data, algorithms, and hardware are heavily siloed by regional laws. For IT architects, Chief Information Officers (CIOs), and professionals conducting strategic technology watches, the Splinternet is the ultimate challenge. You can no longer build one global IT architecture; you must engineer for a deeply divided world.
1. The Three Spheres of AI Governance
The fragmentation of the internet is being driven by three distinct, incompatible philosophies of AI regulation, creating fundamentally different operating environments for enterprise IT.
- The European Union (Rights-Driven): As discussed in Week 40, the EU AI Act prioritizes fundamental human rights, privacy (GDPR), and explainability. Deploying a “High-Risk” AI system here requires rigorous conformity assessments, human-in-the-loop mandates, and strict transparency.
- The United States (Market-Driven): The US approach relies heavily on voluntary frameworks (like the NIST AI RMF) and sector-specific guidelines. The priority is rapid innovation and commercial dominance, allowing tech giants to train massive foundational models with less upfront federal friction, though state-level privacy laws are creating localized complexity.
- China (State-Controlled): China’s AI regulations are the strictest in the world regarding output. Algorithms must undergo security assessments to ensure they reflect “core socialist values.” The state mandates algorithm registries and enforces strict censorship protocols on generative AI outputs, making it impossible to deploy an uncensored Western LLM within its borders.
2. Technological Decoupling and Data Localization
For multinational corporations, these diverging legal frameworks destroy the concept of a single, centralized cloud architecture. An IT manager can no longer license a single instance of OpenAI’s GPT-4 or Google’s Gemini to serve their entire global workforce.
- Data Localization: To comply with regional laws, IT architects must implement strict data localization. European employee data cannot be processed by an AI model hosted on a US server due to sovereignty concerns, and it certainly cannot cross into Chinese data centers.
- Model Forking: Organizations are being forced to “fork” their AI architectures. A global bank must deploy a highly transparent, heavily audited, and privacy-scrubbed Private LLM in Frankfurt for its EU operations, while running a different, more aggressively optimized model in New York, and a completely separate, state-compliant system in Shanghai. This multiplies infrastructure costs, maintenance overhead, and architectural complexity exponentially.
3. The Impact on Global Cybersecurity
The Splinternet does not just complicate compliance; it actively degrades global cybersecurity operations. Cyber threats are inherently borderless, but the defensive tools are increasingly constrained by borders.
- Fragmented Threat Intelligence: Effective security relies on the rapid sharing of Threat Intelligence (IoCs, behavioral patterns, and zero-day signatures) across the globe. As nations restrict cross-border data flows to protect their “sovereign AI” ecosystems, global Security Operations Centers (SOCs) lose their holistic visibility. An attack pattern detected by an AI agent in Europe might be legally blocked from being shared with the US-based incident response team.
- The Export Control War: The physical hardware that powers AI defense—specifically advanced GPUs like the NVIDIA H100—is now heavily sanctioned. The US has banned the export of top-tier AI chips to rival nations. Consequently, global enterprises operating in restricted regions may find themselves unable to procure the compute power necessary to run the advanced, AI-driven EDR and CSPM tools we explored earlier in this series, leaving those regional branch offices highly vulnerable.
4. Strategic IT Management in a Fragmented World
As we conclude this overarching series, the lesson for the modern IT professional is that technical excellence must be matched with geopolitical awareness. The era of “move fast and break things” has been replaced by “move carefully and comply.”
To navigate the Splinternet, IT leaders must adopt a modular, sovereign-by-design architecture:
- Abstract the AI Layer: Do not hardcode specific LLMs into your core business applications. Use API gateways and orchestration layers (like LangChain) so that you can dynamically swap out a US-based model for a European sovereign model based on the user’s geographic location.
- Embrace Edge Computing: By pushing AI processing to the edge (directly onto the user’s device or local network), you bypass many cross-border data transfer legalities. If the data never leaves the localized device, it never triggers international data sovereignty violations.
Conclusion: A Milestone, Not a Finish Line
This article marks the 52nd installment of our technology watch—a full year of exploring the intersection of Artificial Intelligence and cybersecurity. While this wraps up our initial four-part framework and fulfills the core objectives of this year-long research project, it is by no means the end of this blog.
The geopolitical fracturing of the Splinternet proves that AI is not a static technology; it is a continuously evolving strategic battleground. As we move forward, this platform will continue to track, analyze, and decode the future of IT architecture. The first 52 weeks built the foundation. Stay tuned as we continue to navigate the next frontier of enterprise security and technology governance.
