UEBA: Moving Beyond Signatures with AI-Driven Behavioral Analytics
Discover how UEBA uses Machine Learning to baseline user behavior, detect anomalies, and stop insider threats or compromised credentials in real-time.
Introduction: The Shift from “What” to “Who”
Welcome to the first article in our second series: AI-Driven Defense Architectures. Over the past 13 weeks, we explored how threat actors weaponize AI to bypass static security controls. Now, we shift our focus to the Blue Team. How do we defend a network when the malware is constantly mutating and the phishing emails are perfect?
The answer lies in abandoning the search for “known bad” files and focusing instead on “abnormal behavior.” This is the domain of UEBA (User and Entity Behavior Analytics). By leveraging Machine Learning, UEBA systems do not look for malware signatures; they look for deviations from human and machine routines, effectively catching the attacks that traditional tools miss.
1. The Limitation of Rules-Based Security
Historically, Security Information and Event Management (SIEM) systems relied on rigid correlation rules. An administrator would configure a rule: If User X fails to log in 5 times in 1 minute, trigger an alert.
Attackers adapted immediately. They execute “Living off the Land” (LotL) attacks, using legitimate administrative tools (like PowerShell or WMI) with stolen credentials. They also throttle their brute-force attempts to 4 times per minute, staying perfectly under the radar. When an attacker logs in with a stolen, valid password, a rules-based system sees absolutely nothing wrong. The authentication was technically successful.
2. Enter Machine Learning: Baselining the “Normal”
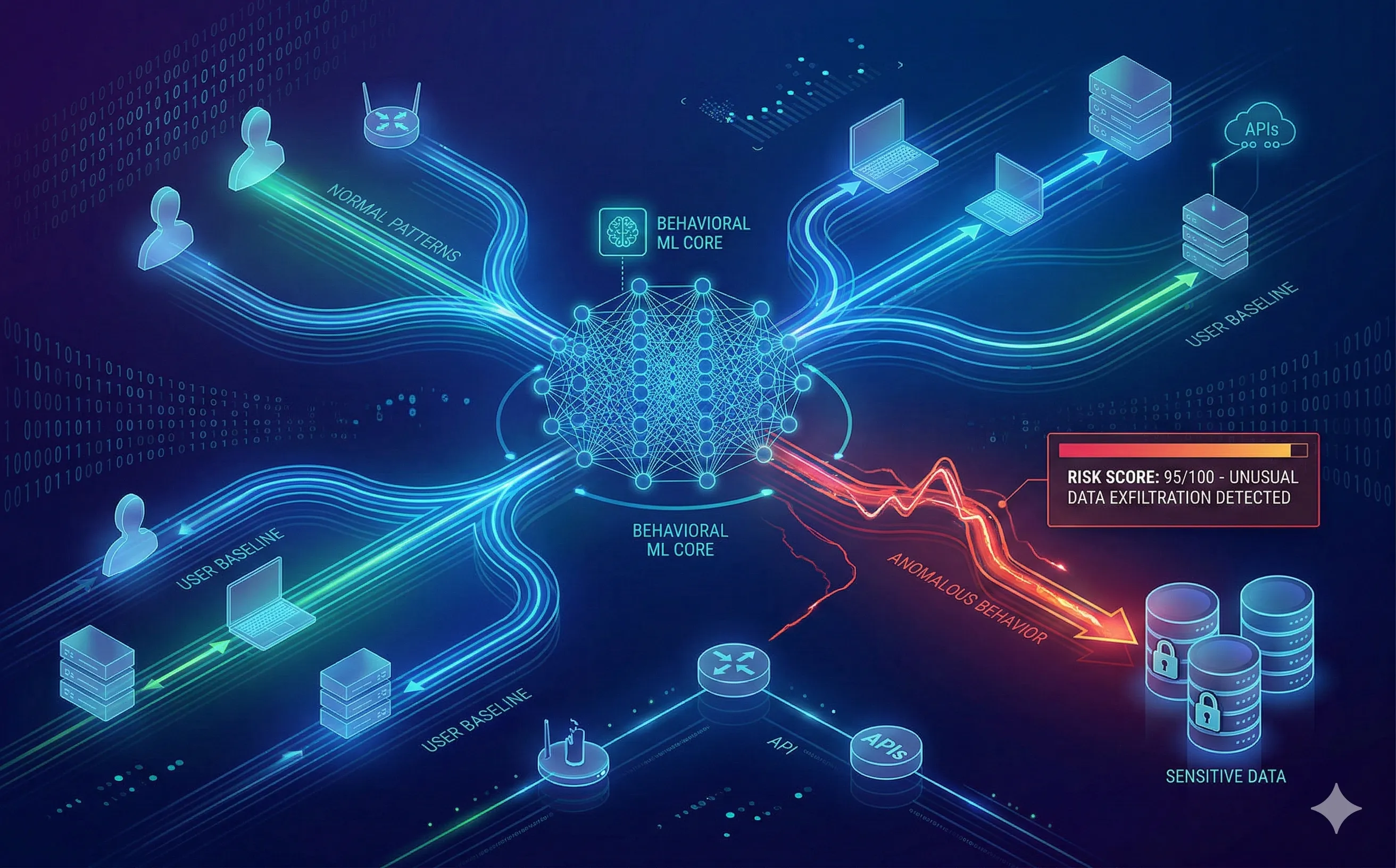
UEBA solves this by using unsupervised machine learning to build a unique behavioral baseline for every single “User” (employees, contractors) and “Entity” (servers, routers, service accounts) on the network.
Instead of static rules, the AI asks dynamic questions:
- Time & Location: Does the CFO usually log in at 3:00 AM on a Sunday from an IP address in a different country?
- Volume & Velocity: Does this marketing intern typically access the source code repository? Do they usually download 50GB of data to an external drive in under ten minutes?
- Peer Group Analysis: The system groups users dynamically. If a developer accesses a specific database, the AI checks if other developers in that same peer group also access it. If not, it flags the anomaly.
3. Real-World Use Cases for UEBA
UEBA is particularly effective against two of the most difficult threats in cybersecurity:
- The Insider Threat: A disgruntled employee decides to steal intellectual property before leaving for a competitor. They have legitimate access to the files, so no antivirus will stop them. However, the UEBA system notices that their data exfiltration volume is 400% higher than their historical 90-day baseline and triggers an immediate alert.
- Compromised Credentials: An attacker successfully phishes an HR manager and uses their credentials to log into the corporate VPN. The attacker then attempts to use
cmd.exeto map network drives. The UEBA system flags this instantly: while the credentials are valid, the behavior (running command-line network mapping) has never been seen from this HR profile before.
4. Risk Scoring and Automated Response
Unlike legacy SIEMs that generate a massive flood of binary alerts (Alert Fatigue), UEBA systems use mathematical Risk Scoring.
Every anomalous action adds points to a user’s risk score.
- Logging in from a new device (+10 points).
- Accessing a sensitive file for the first time (+20 points).
- Attempting a privilege escalation exploit (+60 points).
When the cumulative score crosses a critical threshold (e.g., 90/100), the system doesn’t just alert a human analyst; it can integrate with a SOAR (Security Orchestration, Automation, and Response) platform to take immediate action, such as automatically isolating the infected machine from the network or revoking the user’s authentication tokens.
Conclusion
In a landscape where identities are the new perimeter, knowing who is on your network is no longer enough; you must know exactly how they normally behave. UEBA transforms cybersecurity from a reactive, signature-based discipline into a proactive, data-science-driven practice. It is the foundational layer of any modern Zero Trust architecture.
